Rust has been gaining attention in recent years as a language expected to replace C and C++, due to its memory safety and high performance. While Rust continues to be adopted as a programming language, malware developed using Rust (hereinafter referred to as "Rust malware"), such as Rust variants of SysJoker and the BlackCat ransomware, has also been increasing in recent years. However, knowledge of reverse engineering techniques for Rust...
List of “亀井 智矢(Tomoya Kamei)”
-
-
JPCERT/CC hosted JSAC2026 from January 21 to 23, 2026. JSAC is an annual conference dedicated to advancing the capabilities of security analysts by fostering the exchange of technical knowledge and operational insights related to incident analysis and response. Now in its ninth year, the event incorporated a new training program, expanding the program to three days. Across two days, the conference featured 17 presentations, three workshops, and six lightning talks....
-
On January 21 and 22, 2025, JPCERT/CC held its annual technical conference JSAC, aiming at enhancing the skills and knowledge of security analysts. The conference brought experts in the field of cyber security together to share technical insights related to incident analysis and response. The event marked its 8th year, and it was held as an offline-only event like the previous year. Over the two-day event, there were 18 presentations,...
-
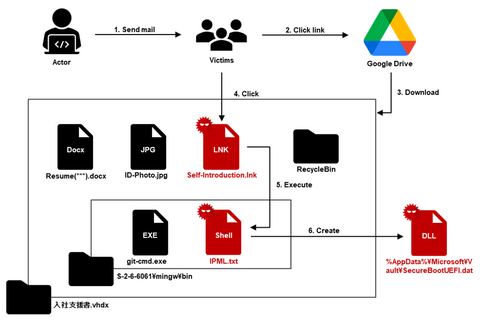
JPCERT/CC has confirmed an attack against an organization in Japan in ...
-
This second blog post features the Main Track talks on the Day 2 of JSAC. XFiles: Large-Scale Analysis of Malicious MSIX/APPX Speakers: Kazuya Nomura, Teruki Yoshikawa, Masaya Motoda (NTT Security Japan) Slides (Japanese) The speakers discussed Microsoft’s new packaged files, MSIX and APPX, which have been exploited in recent years in attack campaigns. They explained the points to focus on when analyzing the structure, operation mechanisms, and characteristics of the...