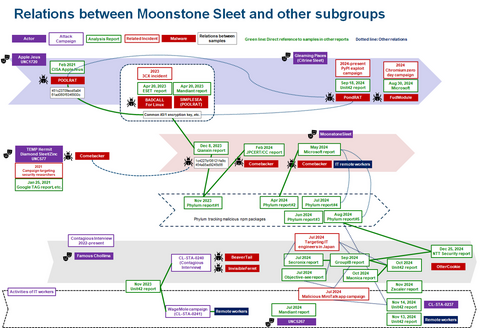
In JPCERT/CC Eyes, we previously reported on attacks conducted by Atta...
List of “Malware”
-
-
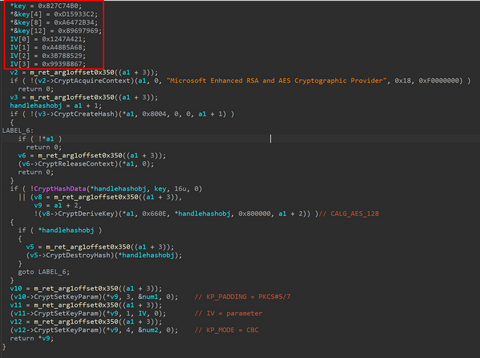
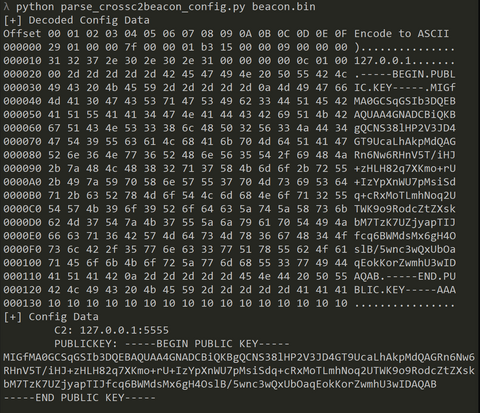
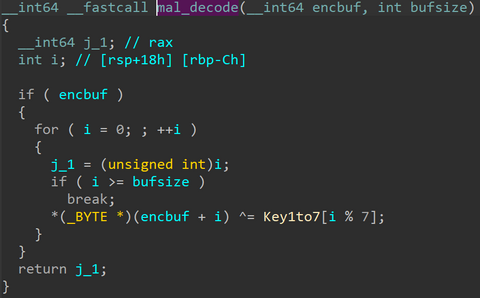
From September to December 2024, JPCERT/CC has confirmed incidents involving CrossC2, the extension tool to create Cobalt Strike Beacon for Linux OS. The attacker employed CrossC2 as well as other tools such as PsExec, Plink, and Cobalt Strike in attempts to penetrate AD. Further investigation revealed that the attacker used custom malware (hereafter referred to as "ReadNimeLoader") as a loader for Cobalt Strike. Information submitted to VirusTotal suggests that this...
-
JPCERT/CC Eyes previously introduced the malware SPAWNCHIMERA and Dslo...
-
In a previous article of JPCERT/CC Eyes, we reported on SPAWNCHIMERA malware, which infects the target after exploiting the vulnerability in Ivanti Connect Secure. However, this is not the only malware observed in recent attacks. This time, we focus on another malware DslogdRAT and a web shell that were installed by exploiting a zero-day vulnerability at that time, CVE-2025-0282, during attacks against organizations in Japan around December 2024. Functionality of...
-
*Please note that this article is a translation of the Japanese versio...
-
In January 2025, Ivanti published an advisory[1] regarding the vulnera...
-
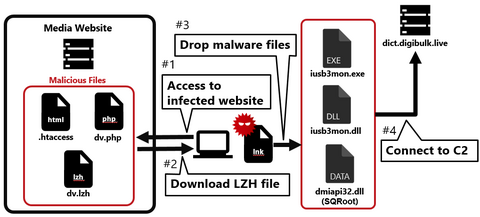
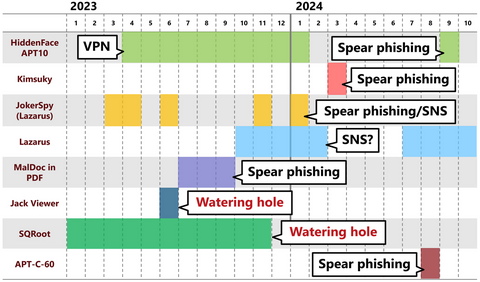
Continuing from the previous article, Part 2 covers another case of a watering hole attack. This time, we will look at the case of a media-related website exploited in 2023. Flow of the attack Figure 1 shows the flow of the watering hole attack. When someone accesses the tampered website, an LZH file is downloaded, and when they execute the LNK file in the LZH file, their PC becomes infected...
-
Nowadays, many people probably recognize exploit of vulnerabilities in publicly exposed assets such as VPN and firewalls as the attack vector. In fact, many security incidents reported to JPCERT/CC also involve such devices. This is because vulnerabilities in VPN devices are exploited not only by APT groups but also by many other groups such as ransomware actors and cyber crime actors, and the number of incidents is high accordingly. As...
-
The difficult part of the initial response to a human-operated ransomware attack is identifying the attack vector. You may already know from recent security incident trends that the vulnerabilities of VPN devices are likely to be exploited, but it often takes much time to investigate because multiple penetration routes are often considered when an incident occurs. Therefore, in order to ensure a smooth initial response, it is important to investigate...
-
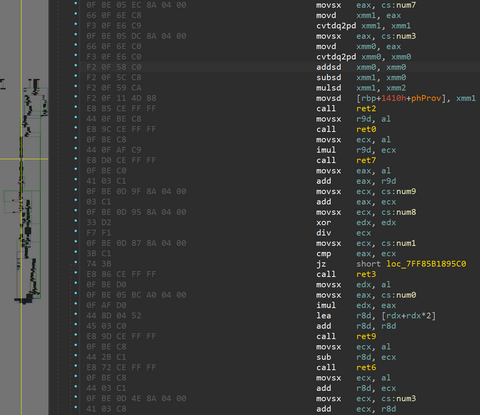
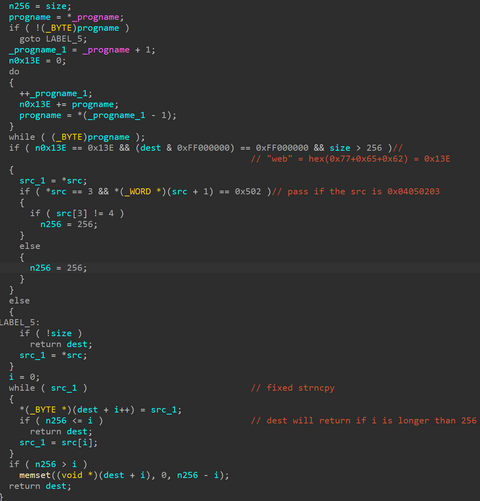
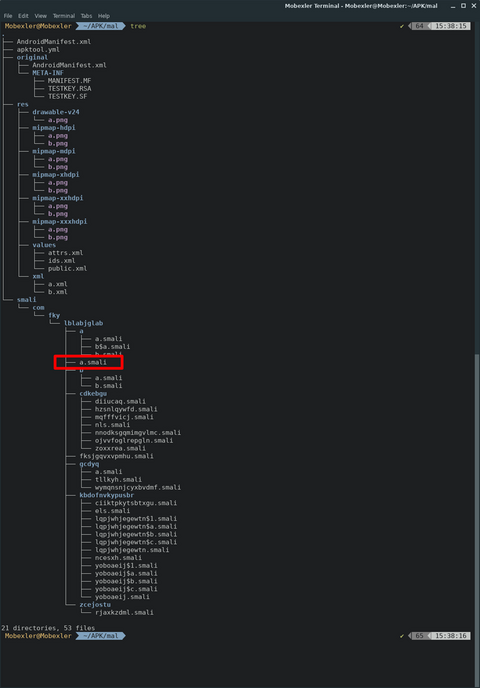
When dynamically analyzing Android malware, it is currently difficult to follow its code using debuggers unlike Windows malware. Although there is a technique [1] to hook a method dynamically by Frida [2], obtaining the in-progress state of the method is still difficult, and since Frida is not a tool dedicated to Android, only limited information can be obtained. In this article, I introduce smali gadget injection technique as a more...