This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports do not include. This article covers the monitoring results for the period October to December 2025. Suspicious Packets Originating from DVR/NVR Devices A review of the number of hosts in Japan sending traffic to Telnet (23/TCP) shows a temporary spike in October, followed by a downward trend beginning...
-
-
JPCERT/CC held the ICS Security Conference 2026 on February 10, 2026. This conference aims to share the current threat landscape surrounding Industrial Control System (ICS) in Japan and abroad, as well as initiatives undertaken by stakeholders in ICS security. It also seeks to help participants strengthen their security measures and establish best practices. Since its launch in 2009, the conference has been held annually, and this year marked the 18th...
-
This TSUBAME Report Overflow series discusses monitoring trends observed by overseas TSUBAME sensors, as well as other activities that are not included in the Internet Threat Monitoring Quarterly Reports. This article covers the monitoring results from July to September 2025. Suspicious packets from domestic NVR products In the main issue of the Internet Threat Monitoring Report, we presented observations of packets originating from TP-Link routers suspected to be infected with...
-
Hello, this is Shihono from the Global Coordination Division. In early March, we traveled to Baku, the capital of Azerbaijan, and had the opportunity to visit five organizations, including CSIRTs and facilities involved in cyber security workforce development. In this article, I would like to introduce an overview of these visits. Azerbaijan, the “Land of Fire,” and Its Capital Baku, the “City of Winds” Baku cityscape and the Caspian Sea...
-
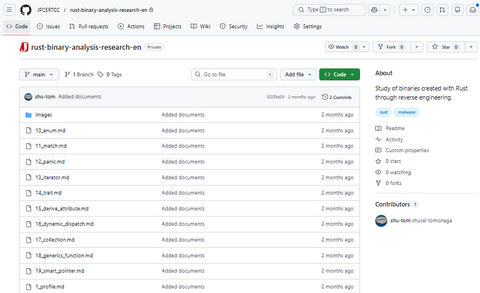
Rust has been gaining attention in recent years as a language expected to replace C and C++, due to its memory safety and high performance. While Rust continues to be adopted as a programming language, malware developed using Rust (hereinafter referred to as "Rust malware"), such as Rust variants of SysJoker and the BlackCat ransomware, has also been increasing in recent years. However, knowledge of reverse engineering techniques for Rust...
-
In this article, we continue our overview of the sessions at JSAC2026....
-
Continuing from the previous report, this second installment introduce...
-
JPCERT/CC hosted JSAC2026 from January 21 to 23, 2026. JSAC is an annual conference dedicated to advancing the capabilities of security analysts by fostering the exchange of technical knowledge and operational insights related to incident analysis and response. Now in its ninth year, the event incorporated a new training program, expanding the program to three days. Across two days, the conference featured 17 presentations, three workshops, and six lightning talks....
-
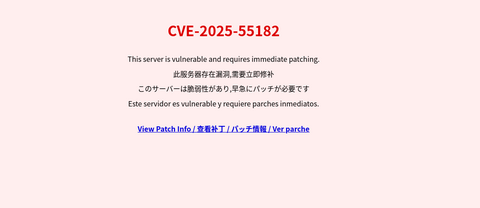
On December 3, 2025 (local time), a vulnerability allowing unauthenticated remote code execution in React Server Components (RSC) (CVE-2025-55182) was disclosed. JPCERT/CC has received multiple incident reports related to this attack. Among them, there was a case in which this vulnerability was exploited by multiple threat actors within a short period of time, resulting in multiple incidents occurring simultaneously, including website defacement. This article demonstrates how rapidly and indiscriminately attackers...
-
In recent years, fileless malware and obfuscation techniques have made it increasingly difficult to detect suspicious activity by scanning files alone. To counter these threats, security researchers and malware analysts actively create and publish detection rules such as Sigma and YARA. However, many existing endpoint security tools rely on unique detection engines, instead of directly using Sigma or YARA. To address this problem, JPCERT/CC released the open-source threat hunting tool...