This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports do not include. This article covers the monitoring results for the period April to June 2025. Fluctuations in packets from Iran, potentially linked to Israel-Iran military conflict Between June 13 and around June 25, 2025, military conflict occurred between Israel and Iran. During this period, fluctuations were observed...
-
-
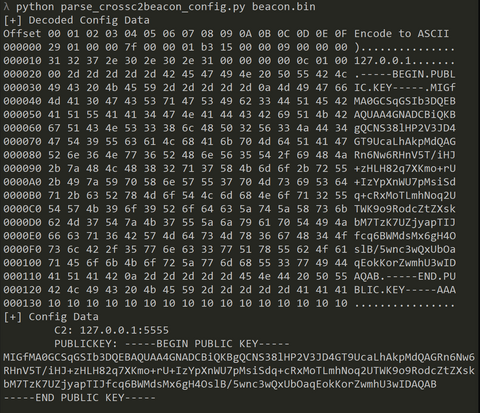
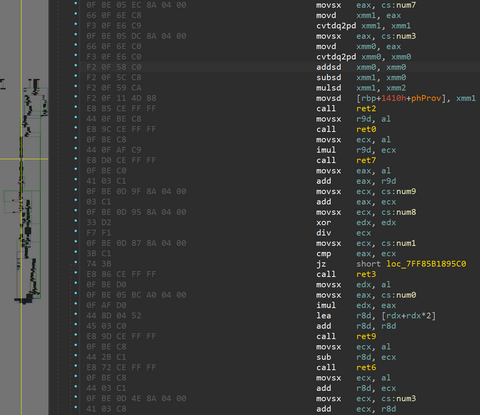
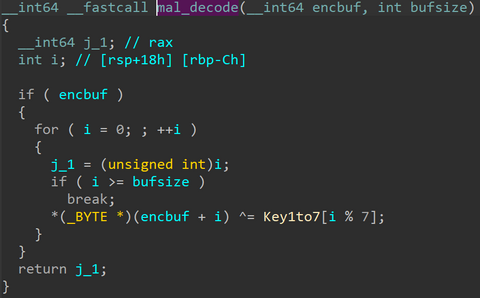
From September to December 2024, JPCERT/CC has confirmed incidents involving CrossC2, the extension tool to create Cobalt Strike Beacon for Linux OS. The attacker employed CrossC2 as well as other tools such as PsExec, Plink, and Cobalt Strike in attempts to penetrate AD. Further investigation revealed that the attacker used custom malware (hereafter referred to as "ReadNimeLoader") as a loader for Cobalt Strike. Information submitted to VirusTotal suggests that this...
-
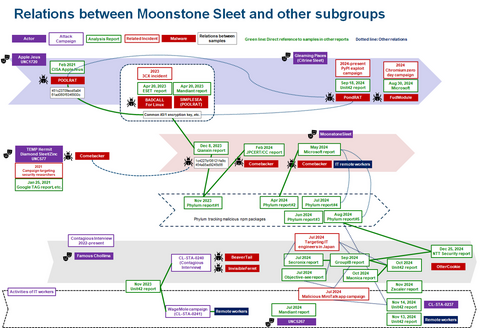
JPCERT/CC Eyes previously introduced the malware SPAWNCHIMERA and Dslo...
-
This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports do not include. This article covers the monitoring results for the period January to March 2025. Trends of Fiscal Year 2024 in Japan At JPCERT/CC, we analyze the data collected from TSUBAME on a daily basis. This time, we would like to focus on incident cases related to...
-
In a previous article of JPCERT/CC Eyes, we reported on SPAWNCHIMERA malware, which infects the target after exploiting the vulnerability in Ivanti Connect Secure. However, this is not the only malware observed in recent attacks. This time, we focus on another malware DslogdRAT and a web shell that were installed by exploiting a zero-day vulnerability at that time, CVE-2025-0282, during attacks against organizations in Japan around December 2024. Functionality of...
-
JPCERT/CC organised ICS Security Conference on 5 February 2025. This event aims to share the current threat to ICS both in Japan and overseas and the efforts of stakeholders in the field, as well as to help participants improve their ICS security measures and establish best practices. The conference started in 2009 and now marks its 17th year. 50 participants attended the event onsite and 511 people through live streaming....
-
Following the previous blog post on the Main Track on Day 2, this article highlights the Workshops and Lightning Talks of JSAC2025. Workshop Handling Threat Intelligence: Techniques of Consuming and Creating Threat Intelligence Speaker: Tomohisa Ishikawa, Tatsuya Daitoku, Hiroyuki Tomiyama (Tokio Marine Holdings, Inc.) Slides (Japanese) Tomohisa, Tatsuya, and Hiroyuki provided a workshop on threat intelligence, giving systematic explanations from the fundamentals to practical applications. They first introduced the core...
-
*Please note that this article is a translation of the Japanese versio...
-
This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports does not include. This article covers the monitoring results for the period of October to December 2024. Observation of reflection packets from Websites of organizations in Japan At JPCERT/CC, we analyze the data collected from TSUBAME on a daily basis. We sometimes observe packets from websites responding to...
-
Continuing from the previous blog article, this entry introduces the presentations on the 2nd day of JSAC2025. Observation of phishing criminal groups related to illegal money transfers and Mizuho Bank’s countermeasures -Fighting against phishing site malware ‘KeepSpy’- Speaker: Tsukasa Takeuchi, Takuya Endo, Hiroyuki Yako (Mizuho Financial Group) Slides(English) Tsukasa, Takuya, and Hiroyuki presented Mizuho’s efforts to address phishing attacks, including the analysis of exploited malware and the criminal groups behind...