In June 2017, JPCERT/CC released a report “Detecting Lateral Movement through Tracking Event Logs” on tools and commands that are likely used by attackers in lateral movement, and traces that are left on Windows OS as a result of such tool/command execution. After the release, we received a lot of feedback on the report, and until now we had been working on the revision based on the comments. Today, we...
List of “Report”
-
-
Hello again, this is Shusei Tomonaga from the Analysis Center. Event log analysis is a key element in security incident investigation. If a network is managed by Active Directory (hereafter, AD), can be identified by analysing AD event logs. For such investigation, it is quite difficult to conduct detailed analysis in AD event viewer; it is rather common to export the logs to text format or import them into SIEM/log...
-
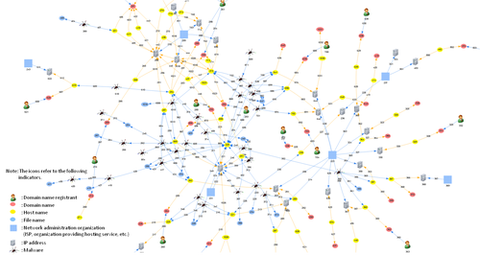
JPCERT/CC has been seeing a number of APT intrusions where attackers compromise a host with malware then moving laterally inside network in order to steal confidential information. For lateral movement, attackers use tools downloaded on infected hosts and Windows commands. In incident investigation, traces of tool and command executions are examined through logs. For an effective incident investigation, a reference about logs recorded upon tool and command executions would be...
-
Hello again, this is Shusei Tomonaga from the Analysis Center. In Windows OS, various commands (hereafter “Windows commands”) are installed by default. However, what is actually used by general users is just a small part of it. On the other hand, JPCERT/CC has observed that attackers intruding into a network also use Windows commands in order to collect information and/or to spread malware infection within the network. What is worth...
-
Hi, this is You 'Tsuru' Nakatsuru again from Analysis Center. This past summer, I joined the “Security Camp 2015” in Japan as a trainer for a malware analysis training course, which was held for students aged 22 and under living in Japan, with the aim of discovering top, young talents. This blog entry is to introduce the malware analysis training materials which I used at Security Camp 2015 as below....
-
You may well have heard of the May cyber attack in Japan against the Japan Pension Service – a high-profile case seen in the first half of this year, where 1.25 million cases of personal data was exposed. According to the Japan Pension Service, the data leaked included names and ID numbers, and for some cases, dates of birth and home addresses. The official reports(1) say that the massive leak...
-
Hi! I’m Takuho Mitsunaga from Watch and Warning Group. I am pleased to announce that JPCERT/CC has just released a report "Investigation Report Regarding Security Issues of Web Applications Using HTML5 (English version)." As mentioned in the previous posts - JPCERT/CC at “CODE BLUE” and Presenting HTML5 security at OWASP AppSec APAC 2014, through publishing a report (Japanese version), we have worked to point out the issues and raise awareness...