Hello, I am Katsuhiro Mori from Cyber Metrics Line, Global Coordination Division. JPCERT/CC released ”Mejiro” (Internet risk visualisation service) English website in August 2018. This web service collects publicly available risk data on risk factors existing on the Internet and provides index for each economy. To promote the use of this tool service and cyber space clean-up activities, I went to Mongolia and Indonesia recently. What is Mongolia like? When...
List of “2018”
-
-
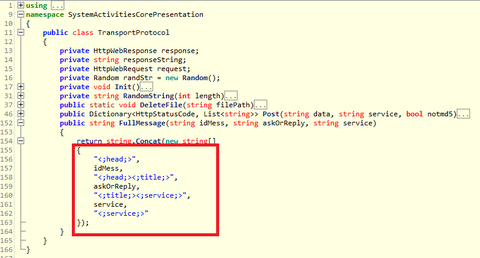
In a previous article we have introduced malware ‘TSCookie’, which is assumedly used by an attacker group BlackTech. We have been observing continuous attack activities using the malware until now. In the investigation of an attack observed around August 2018, we have confirmed that there was an update in the malware. There are two points meriting attention in this update: Communication with CC server Decoding configuration information This article will...
-
Greetings from JPCERT/CC! Thank you for visiting JPCERT/CC blog. We are happy to announce that we now have a new blog site "JPCERT/CC Eyes". The new URL is https://blogs.jpcert.or.jp/en/. The previous articles published on the existing platform have been tranferred to this new site. We will continue to provide our technical insights and latest cyber security trends on this site with the new fresh look. Thank you and stay tuned!...
-
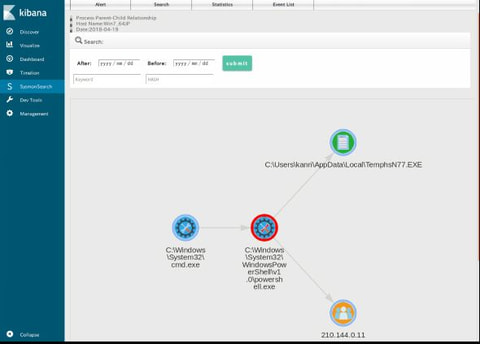
In recent sophisticated cyber attacks, it is common to observe lateral movement, where a malware- infected device is used as a stepping stone and further compromise other devices in the network. In order to investigate the compromised devices, it is necessary to retain detailed logs of the applications that run on the device on a daily basis. One of the well-known tools for this purpose is Sysmon [1] from Microsoft,...
-
JPCERT/CC has observed some Japanese organisations being affected by cyber attacks leveraging “Cobalt Strike” since around July 2017. It is a commercial product that simulates targeted attacks [1], often used for incident handling exercises, and likewise it is an easy-to-use tool for attackers. Reports from LAC [2] and FireEye [3] describe details on Cobalt Strike and actors who conduct attacks using this tool. Cobalt Strike is delivered via a decoy...
-
Some malware is designed to run on multiple platforms, and most commonly they are written in Java. For example, Adwind malware (introduced in a past article) is written in Java, and it runs on Windows and other OS. Golang is another programming language, and it is used for Mirai controller, which infects Linux systems. This article introduces the behaviour of WellMess malware based on our observation. It is a type...
-
In a past article, we introduced TSCookie, malware which seems to be used by BlackTech[1]. It has been revealed that this actor also uses another type of malware “PLEAD”. (“PLEAD” is referred to both as a name of malware including TSCookie and its attack campaign [2]. In this article, we refer to “PLEAD” as a type malware apart from TSCookie.) PLEAD has two kinds – RAT (Remote Access Tool) and...
-
Today, I would like to introduce an activity at the Vulnerability Coordination Group of JPCERT/CC.It is a method to describe a vulnerability using Vulnerability Description Ontology (VDO). JPCERT/CC receives software vulnerability information from domestic and overseas reporters, then coordinates them in between the vendor/developer and the reporter. While there is a vulnerability reporting template, vulnerability itself is described in a free format. Reporter can describe about a vulnerability in a...
-
JPCERT/CC has been coordinating and disclosing software vulnerabilities under the "Information Security Early Warning Partnership" since 2004. We have coordinated and disclosed over 1,500 vulnerabilities with developers as of the end of 2017. The "Information Security Early Warning Partnership" has a guideline that serves as a framework for how vulnerabilities are coordinated within Japan. An overview of the framework including how reported vulnerabilities are coordinated and disclosed is provided at...
-
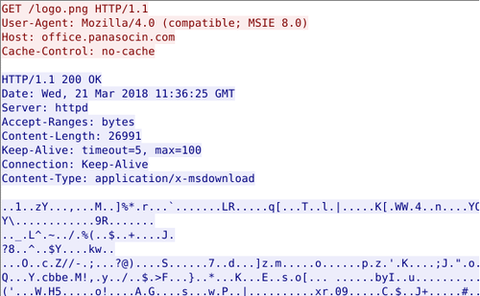
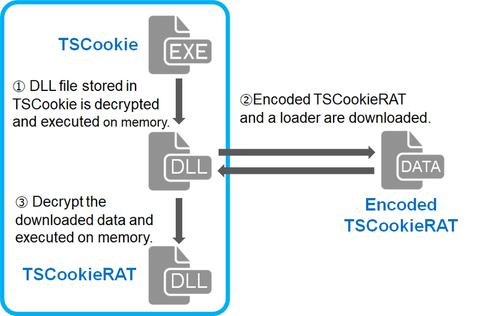
Around 17 January 2018, there were some reports on the social media about malicious emails purporting to be from Ministry of Education, Culture, Sports, Science and Technology of Japan [1]. This email contains a URL leading to a malware called “TSCookie”. (Trend Micro calls it “PLEAD” malware [2]. Since PLEAD is also referred to as an attack campaign, we call this malware TSCookie in this article.) TSCookie has been observed...