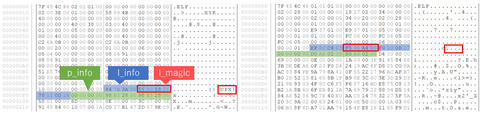
Malware targeting Windows OS (PE format) has a variety of obfuscation and packing techniques in place so that they complicate the code analysis processes. On the other hand, there are only a few types of packing techniques for Linux-targeting malware (ELF format), and it is mainly UPX-based. This blog article explains the details of Anti-UPX Unpacking technique, which is often applied to Linux-targeting malware. Malware with Anti-UPX Unpacking Technique The...
List of “IoT”
-
-
Greetings. This is Aki Hitotsuyanagi from ICS Security Response Group. Today, I would like to introduce to you our new document, “Cyber Security First Step for Introducing IIoT to the Factory -Security Guide for Businesses Implementing IIoT-“.The original Japanese version of this document was released August 2018 and has been receiving favorable reviews. IIoT, or Industrial Internet of Things refers to use of IoT in industrial sectors. For example, using...