ICS Security Conference 2020 Report -Part2-
Following the previous article, we continue with the summary of the second half of the ICS Security Conference 2020 program.
The Trend in Standardization of ICS Security System -The Introduction and Updates of IEC 62443-
By Junya Fujita (Center for Technology Innovation, Control Platform Research Development, Hitachi, Ltd)
In this presentation, the overview of and the updates on IEC 62443, which is the standard in ICS security, and related certification system were introduced.
Mr. Fujita began his talk by sharing his understanding that the necessity of ISC security is widely and increasingly recognized these days. IEC 62443 series and other standards have been more and more developed and adopted to ensure the security of ICS.
IEC 62443 series is a set of standards that prescribes recommended measures to assure the security of Industrial Automation and Control System (IACS). It is one of the particularly remarkable standards in the field of ICS security since the governments and business organizations from a wide range of industrial areas already reference and utilize the standards. Mr. Fujita argued that IACS is not only a matter of hardware and software system per se but also involves the operations and operators of the system. During the presentation, the structure of IEC 62443, summary and updates of each part , and the latest related topics were also introduced with details. At present, IEC 62443 series is being revised actively, and at the same time, it is getting more difficult to maintain the consistency among the series.
He also mentioned that a program for certification was developed to verify the compliance with IEC 62443’s requirements. This initiative is not only for systems and products, and there are certification systems available for the development process, organizational security management, and employees involved.

Effective Use of ES-C2M2 (Maturity-level Self-assessment of ICS Security Management)
By Gen Kinoshita (Researcher,Vulnerability Countermeasures Group, IT Security Countermeasures department, IT Security Center (ISEC), Information-technology Promotion Agency, Japan (IPA))
In this presentation, the overview and usage of ES-C2M2, the maturity model of security management, were introduced.
ES-C2M2 stands for Electricity Subsector Cybersecurity Capability Maturity Model Program, and it was issued by the United States Department of Energy (DoE). ES-C2M2 is a security management self-assessment program originally designed for electric power industry in the United States. This program can be useful for an organization to assess the maturity level of security measures and techniques of its own. The program also assists the organization in setting a goal and/or priority for future improvements. IPA translated the core C2M2 and the implementation guidance into Japanese, and the documents are available on IPA’s website.
The maturity model consists of 10 domains, and each domain has 37 goals. Furthermore, those goals contain 312 practices each. An organization can self-evaluate their “Maturity Indicator Level (MIL)” of each domain on the scale of 0 to 3, by rating its maturity level of each practice on a four-level scale. The result can be shown in a visually understandable manner with a donut chart. Mr. Kinoshita argued that organizations in a wide range of industries would find ES-C2M2 a helpful and practical self-evaluation tool in identifying the domains that require improvements.

ICS Security Measures in Semiconductor Manufacturing
By Akio Oka (CISO/Executive Officer, Kioxia Corporation)
Mr. Oka, the CISO of Kioxia Corporation’s (the former Toshiba Memory Corporation), discussed the company’s practices as well as challenges in cyber security for their domestic production facilities.
*The content of the presentation is shared with the conference participants only.

Murata Manufacturing’s Cyber Security Practices for Production Area
By Takahiro Sakamori (Senior Manager, Information Technology Literacy Promoting Section, Information Technology Planning Department, Murata Manufacturing Co., Ltd.)
Murata Manufacturing is a world-wide electronic component manufacturer, and Mr. Sakamori discussed the company’s practices for cyber security reinforcement, challenges in improving the security of production area, and their plans for the future.
*The content of the presentation is shared with the conference participants only.

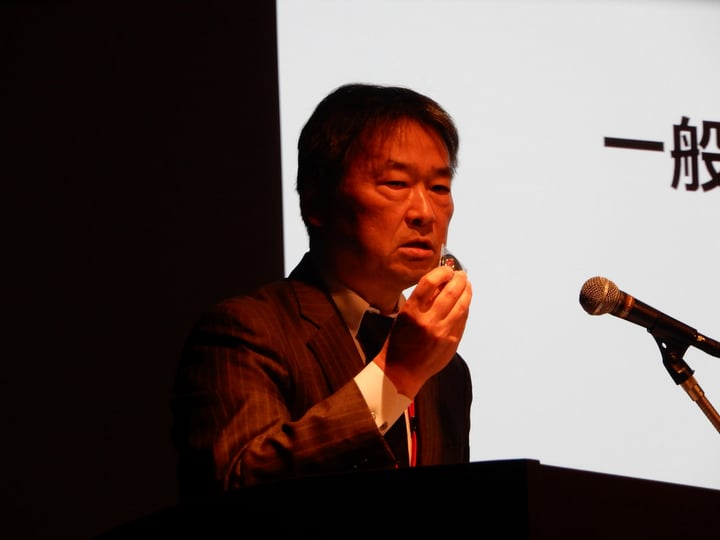
Closing Remarks
This year, JPCERT/CC’s challenge coin was presented to each conference speaker with gratitude. Koichi Arimura, Managing Director of JPCERT/CC, showed the challenge coin and encouraged the audience to apply for the CFP next year. He closed his remarks by expressing his gratitude to the speakers, who shared their information, knowledge, and insights, as well as to the audience, who filled the conference venue to capacity.
In Closing
Many people participated in ICS Security Conference this year, and we saw the increasing interests and concerns in ICS security. We hope that the next conference grows to a more helpful and productive event for everyone involved in ICS security. We would like to thank everyone who participated in the conference and the readers of this report.
-Miki Ikegami
(Translated by Takumi Nakano)

