TSUBAME Report Overflow (Oct-Dec 2021)
This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports does not include. This article covers the monitoring results for the period of January to March 2022. The scan trends observed with TSUBAME sensors in Japan are presented in graphs here.
Scan packets to GRE increased
Table 1 shows the top 5 packets sent from IP addresses in Japan, which the Internet Threat Monitoring Quarterly Report did not cover. Packets to Generic Routing Encapsulation (GRE) were observed the most. These packets were observed by a wide range of sensors.
Table 1: Top 5 protocols/port numbers of TSUBAME sensors in Japan that observed packets the most
| Rank | Protocols/Port numbers |
|---|---|
| 1 | GRE |
| 2 | 23/TCP |
| 3 | 445/TCP |
| 4 | 37215/TCP |
| 5 | 8545/TCP |
GRE is a tunneling protocol that transmits encapsulated data through GRE tunnels. The result of the packet captures that TSUBAME sensors observed are shown in Figure 1 although it is not clear whether they are meaningful. (Some information about TSUBAME sensor is masked.)
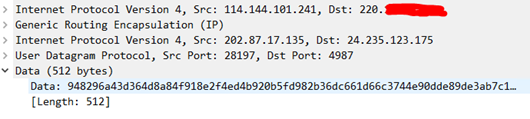
Figure 1: Sample of observed GRE packets
We checked the sources of GRE packets using data from scan data service providers such as SHODAN and Censys, but we found nothing in common such as specific operating systems or software running. However, we confirmed that web servers and IoT products such as surveillance cameras and recorders were running at some of the senders. As a part of our incident response, JPCERT/CC is notifying the administrators of those IP addresses in Japan which sent GRE packets.
Comparison of the observation trends in Japan and overseas
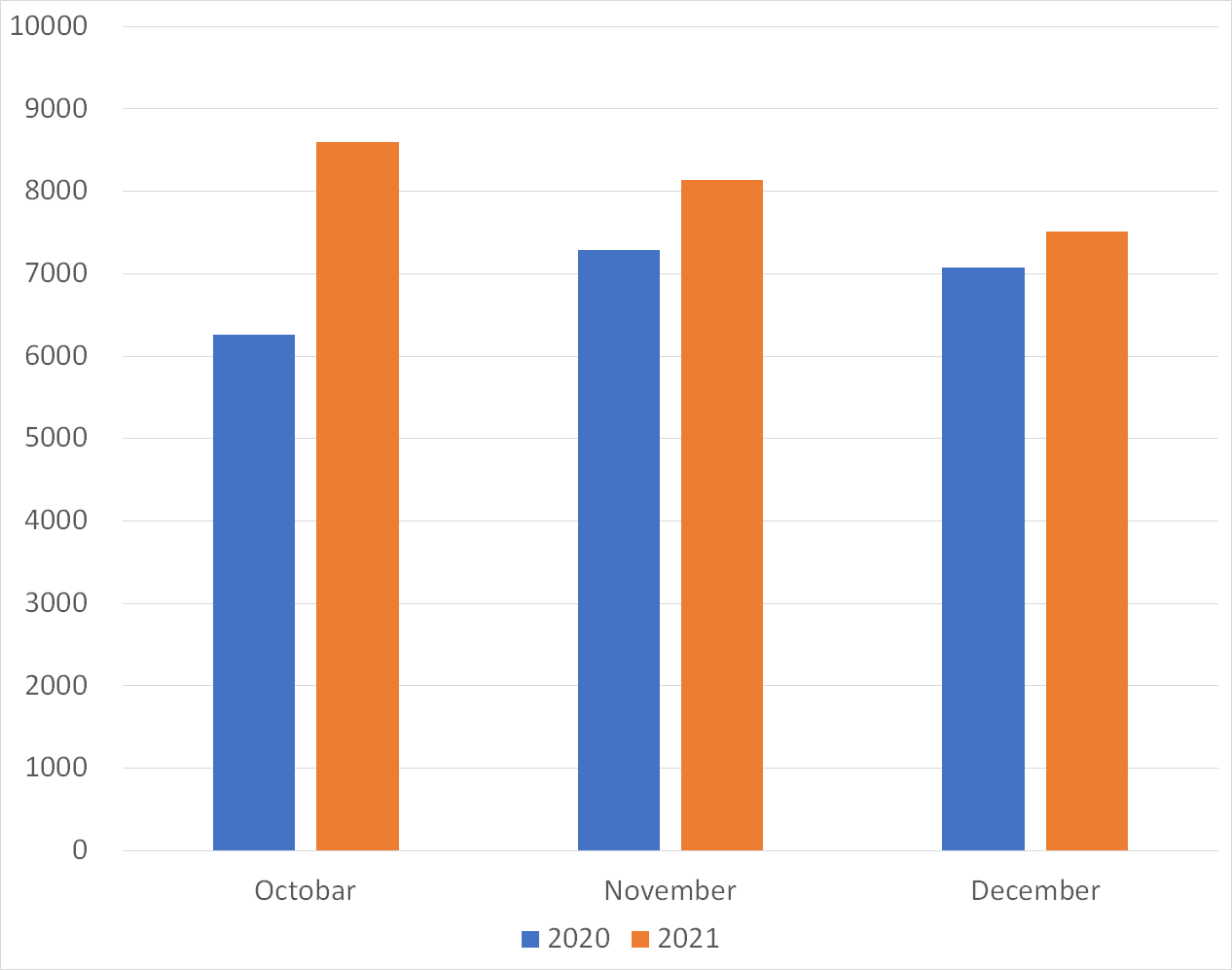
Figures 2 and 3 show a monthly comparison of the daily average number of packets received by a single sensor in Japan and overseas. More packets were observed in the overseas sensors than in the domestic sensors. You can also see that more packets were observed by sensors both in Japan and abroad in every month compared to the same months in the previous year.
 |
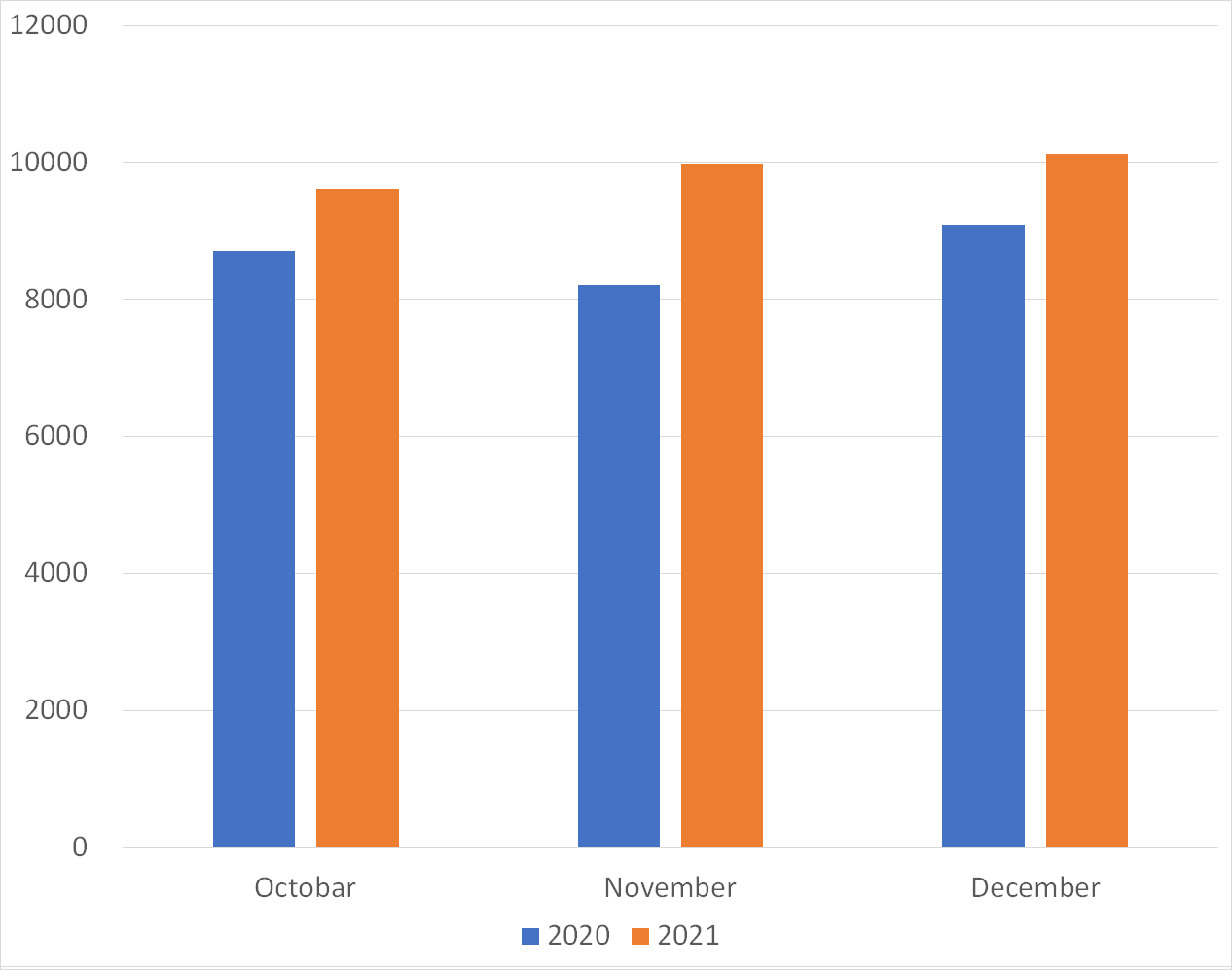 |
| Figure 2: Average number of packets to domestic sensors | Figure 3: Average number of packets to overseas sensors |
Comparison of monitoring trends by sensor
A global IP address is assigned to each TSUBAME sensor. Table 2 shows the top 10 ports of each sensor which received packets the most. 6379/TCP, 23/TCP, 22/TCP, etc., which Redis uses, were observed by all sensors. There is no significant difference in observation results between sensors in Japan and overseas while the order of ports is slightly different. This suggests that these protocols are being scanned in a wide range of networks.
Table 2: Comparison of top 10 packets by domestic and overseas sensors
| #1 | #2 | #3 | #4 | #5 | #6 | #7 | #8 | #9 | #10 | |
| Domestic sensor1 | 123/UDP | 6379/TCP | 5555/TCP | 23/TCP | 22/TCP | 445/TCP | ICMP | 2375/TCP | 443/TCP | 80/TCP |
| Domestic sensor2 | 6379/TCP | 23/TCP | 123/UDP | 22/TCP | 445/TCP | 443/TCP | 2375/TCP | 80/TCP | 2376/TCP | 1433/TCP |
| Domestic sensor3 | 6379/TCP | 23/TCP | 22/TCP | 445/TCP | 443/TCP | 37215/TCP | 80/TCP | 5060/UDP | 2375/TCP | 1433/TCP |
| Overseas sensor1 | 6379/TCP | 23/TCP | 22/TCP | 5060/UDP | 80/TCP | 5555/TCP | 1433/TCP | 443/TCP | GRE | 81/TCP |
| Overseas sensor2 | 23/TCP | 6379/TCP | 445/TCP | 22/TCP | 139/TCP | 1433/TCP | 5060/UDP | 80/TCP | 443/TCP | 5555/TCP |
| Overseas sensor3 | 445/TCP | 139/TCP | 6379/TCP | 23/TCP | 22/TCP | 123/UDP | 5555/TCP | ICMP | 5060/UDP | 2375/TCP |
In closing
Monitoring at multiple points makes it possible to see whether some trends are unique to a particular network. We observed scan packets for Redis both in Japan and other regions, and we are preparing to provide information to CSIRTs of those regions, hoping that we can make some changes. As for GRE, there is no public information addressing this issue at this point. We will figure out this trend based on the information in the feedback we receive. In this quarter, we did not publish any special security alert or other information, but the attention should be paid to the above issue regarding Redis when using the Internet. We will continue to publish blog articles as the Internet Threat Monitoring Quarterly Report becomes available every quarter. We will also publish an extra issue when we observe any unusual change. Your feedback on this series is much appreciated. Please use the below comment form to let us know which topic you would like us to introduce or discuss further. Thank you for reading.
Keisuke Shikano (Translated by Takumi Nakano)

