FAQ: Malware that Targets Mobile Devices and How to Protect Them
Since around 2018, JPCERT/CC has observed an increasing number of malicious activities that target mobile devices such as infection of information theft malware and redirection to phishing sites. JPCERT/CC has received reports from overseas security organizations regarding mobile devices in Japan infected with malware, and a large number of infected mobile devices have been confirmed. In addition, the number of reports of malicious websites used in such attacks on mobile devices has increased to more than 5,000 recently. (Figure 1).
Concerned about the fact that many mobile device users are suffering from malware infection and phishing, JPCERT/CC created a list of frequently asked questions on how to prevent and respond to malware infection on mobile devices. If you suspect that your mobile device has been infected with malware, or if you receive a notification of malware infection, please refer to the following information to take necessary actions.
Although this article addresses the malware MoqHao and TianySpy, which have recently been targeting mobile device users in Japan, and countermeasures against them, the content can be used as a general security measure for mobile devices.
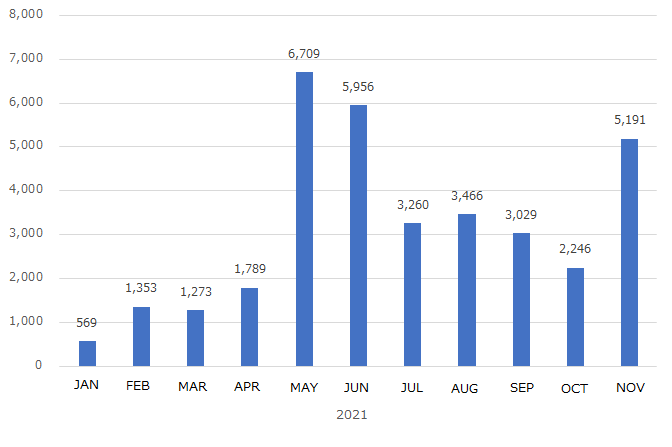
Figure 1. The number of URLs used in attacks targeting mobile devices (based on reports to JPCERT/CC)
Table of Contents
1. What kind of techniques are used for malware infection?
2. What does a suspicious SMS look like?
3. How can I recognize a suspicious SMS or fake website?
4. What should I do if I receive a suspicious SMS?
5. What happens if I access a link in a suspicious SMS?
6. How does malware infect my mobile device? (Android OS)
7. How does malware infect my mobile device? (iOS編)
8. What happens if my device gets infected with malware?
9. How can I check if my device is infected with malware?
10. What should I do if I learn that my device is infected with malware?
11. What should I do to prevent malware infection?
1. What kind of techniques are used for malware infection?
We have confirmed many cases of malware infection by accessing a URL in a suspicious SMS. When a victim accesses such a URL, it leads to a malicious website, and a message asking the victim to download a malicious app (malware) appears. If they download and install the app as instructed, their device will be infected with malware.
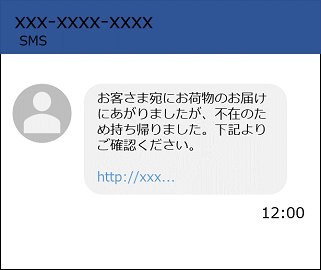
Figure 2. An example of suspicious SMS
2. What does a suspicious SMS look like?
There are several types of suspicious SMS messages. For example, some of them are disguised as a delivery notice, and others guide the recipients to download a fake reservation app (malware) for COVID-19 vaccination. The recipients might access the links in such messages.
Note that such suspicious SMS may be sent from the mobile devices of other victims’ devices infected with malware
“Your package is undelivered because you were not at home. Please check below.”
“Yamato Transport attempted to deliver your package, but it is undelivered because the address is unknown. Please check below.”
“Sagawa Express attempted to deliver your package, but it is undelivered because the address is unknown.”
“Please install the app to make an appointment for a free COVID-19 vaccination”
“This is ‘docomo’ customer service center. Your payment has not been confirmed, yet. Please check.”
“This is ‘au’ customer service center. We have not received a confirmation of your payment. Please confirm.
“[Notice from SoftBank] Your data use exceeded the limit. Please check as soon as possible.”
* The original text is in Japanese, and the English translation is roughly as follows.
3. How can I recognize a suspicious SMS or fake website?
It is important to avoid accessing the URL in the SMS. Instead, you should check the service from its official website.
In the past, unnatural Japanese expressions were sometimes used. However, it is difficult to identify a suspicious SMS or fake website URL from their texts or URL these days. In addition, fake websites use the logo of the official service, making it difficult to determine from the websites’ appearance whether they are fake or not.
4. What should I do if I receive a suspicious SMS?
It is recommended to avoid accessing the URL in the suspicious SMS and delete the message without any further action. If the contents of the message are from a company you want to check, you should visit the company's official website instead of accessing the URL in the SMS.
5. What happens if I access a link in a suspicious SMS?
It will lead you to a fake website and prompt you to download a malicious app (malware). Otherwise, you may be redirected to a phishing site. To avoid accidentally installing a malicious app (malware) or becoming a victim of phishing, make sure to avoid accessing the URL in suspicious SMS messages.
6. How does malware infect my mobile device? (Android OS)
If you download and install a malicious app (malware), your device gets infected with malware. The following example shows the steps how a malicious app (malware) disguised as “docomo Anshin Security” is downloaded. Products and services to be used for such fake websites and apps change over time.
Accessing the URL in the suspicious SMS leads you to a fake website disguised as “docomo Anshin Security*” (Figure 3). In the case you accidentally access the fake site, make sure to close the browser. Accessing the fake site alone does not infect your device with malware.
* A security service by docomo

Figure 3. An example of accessing a fake website and downloading a malicious app (malware).
The fake site shows a page that prompts you to install a malicious app (malware). If you tap “Download,” it shows a pop-up message asking you to confirm the download. (Figure 3. Screenshot #3 of the fake website). If you tap “Download,” a malicious app (malware) is downloaded to your mobile device.
At this point, your mobile device is not yet infected with the malware. There is no problem if you delete the file without any other action.
1. Tap “Files” on the home screen.
2. Select “Download” to open the “Download” folder.
3. Touch and hold the downloaded malicious file, and then tap the trash can icon in the upper right corner.
*The file manager app may look different depending on the mobile device you use.

Figure 4: Deleting the malicious file.
When you tap “Download and Open,” the browser shows a warning message saying, “Unknown apps cannot be installed” (Figure 5. Screenshot #1 of the mobile device). If you tap “Setting,” enable “Allow apps from this provider” (Figure 5. Screenshot #2), and then tap “Install,” your mobile device installs the malicious app (malware) and gets infected with the malware.
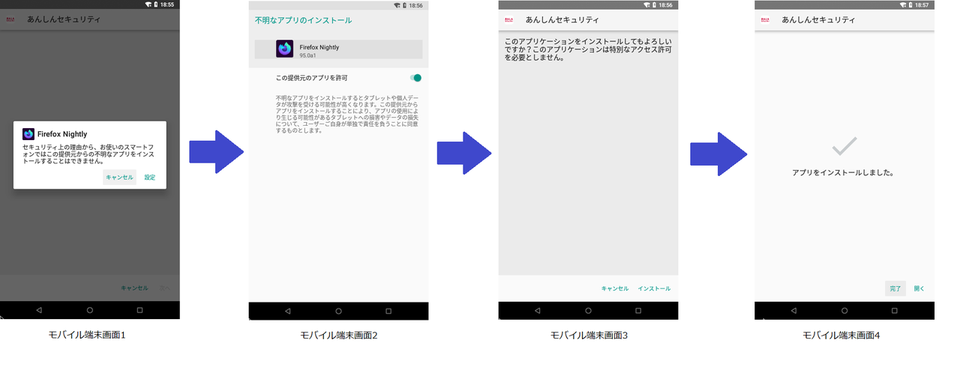
Figure 5. An example of installing a downloaded malicious app (malware) on a mobile device
7. How does malware infect my mobile device? (iOS).
There are two patterns in attacks targeting iOS (iPhone). In one of them, accessing the URL in a suspicious SMS leads to a phishing site disguised as a login page for AppleID or mobile carriers. In the other pattern, a fake site prompts you to download a malicious app (malware), just like the Android OS.
The fake site that guides you to download a malicious app (malware) first asks you to download and install a malicious configuration profile on your device. Such profile allows you to download apps from outside the App Store. If you proceed to download and install a malicious app (malware) following the instruction, your device gets infected with malware.
If you accidentally access the URL in the suspicious SMS, you should close your browser without entering any credentials or downloading an app from outside its official website.
8. What happens if my device gets infected with malware?
A mobile device infected with malware communicates in background with a server the attacker prepared (C2 server). When the malware receives a command from the attacker, it sends the information stored in the mobile device to the C2 server.
- Send phonebook information (registered names and phone numbers) to a C2 server
- Send SMS messages stored in the device to a C2 server
- Send suspicious SMS messages without the user’s permission using the infected mobile device’s phone number
- Disable the infected device’s notifications
- Open a phishing site
- Open a phishing site disguised as an online banking app installed on the infected mobile device (if any).
9. How can I check if my device is infected with malware?
When you want to know whether your device is infected, or you accidentally install malware, checking the below points may be helpful depending on the mobile carrier you use and your environment.
- Check the list of apps to find any app you do not remember installing or have accidentally installed
- Check for malware infection by running a full scan with an antivirus app* (Android OS)
- Check for any suspicious configuration profile you have accidentally installed or do not remember installing (iOS)
- Check your mobile phone bill to find any charge you do not remember
- If your mobile carrier sets a limit on the maximum number of SMS sent per day, you may be notified that your devices have sent too many SMS messages
- Check your SMS “Sent” box for any message you do not remember sending
- If you receive a notification from an account service you use regarding password change you do not remember, it might indicate malware infection
- Check your monthly mobile phone bill for any charge or service you do not remember
* Antivirus apps recommended by mobile carriers or distributed on Google Play
10. What should I do if I learn that my device is infected with malware?
Method 1: How to remove a malicious app (malware) using an anti-virus app
Install and use an antivirus app recommended by mobile carriers or distributed on Google Play.
Method 2: How to remove a malicious app (malware) manually
- Go to “Settings” -> “Apps” to display the list of installed apps
- Check for any app you do not remember installing or any malicious app (malware) you have accidentally installed
- If you find any, tap the app and select “Uninstall” from “App Info” to delete it.

Figure6. Uninstalling a malicious app (malware)
Method 1: How to remove a malicious app (malware)
- Open "Settings" -> "General" -> "iPhone Storage"
- Check the list of apps to see if there are any apps that you don't recognize or any malicious apps (malware) that you have installed.
- Select the app you want to remove and tap "Remove App"
Method 2 How to remove a malicious profile
iOS14 and older
- Go to “Settings” -> “General” -> ”Manage Profile and Device”
- Select and delete the configuration profile you have accidentally installed
» Apple: Install or remove configuration profiles on iPhone
https://support.apple.com/en-us/guide/iphone/iph6c493b19/ios
iOS15
- Go to “Settings” -> “General” -> “Manage VPN and Device”
- Select and delete the configuration profile you have accidentally installed
Refer to the website of your service provider for further details. The operation may differ depending on your environment.
If malware infection is confirmed, the information on the mobile device can be misused. Please also check the following items.
Check for any payment you do not remember making with your carrier payment, credit card, or other payment services.
Change your password for your Internet banking services, SNS accounts, Google accounts, etc.
Inform the service provider of the suspected information-fraudulent service that you are a victim of a phishing scam, and depending on the instructions, change your PIN, reissue your card, or change your ID and password for shopping sites or providers.
11. What should I do to prevent malware infection?
Note the following items to protect your mobile device from malware infection.
- Do not access a URL in SMS (Check the official website instead)
- Do not allow apps from unknown sources to be installed
- Do not allow configuration profiles to be installed easily
- It is recommended to download and install apps only from Google Play and App Store
- Install an antivirus app
Yuta Fuchikami
(Translated by Takumi Nakano)

