TSUBAME Report Overflow (Apr-Jun 2022)
This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports does not include. This article covers the monitoring results for the period of April to June 2022. The scan trends observed with TSUBAME sensors in Japan are presented in graphs here.
Changes in Mirai-type packets in Japan
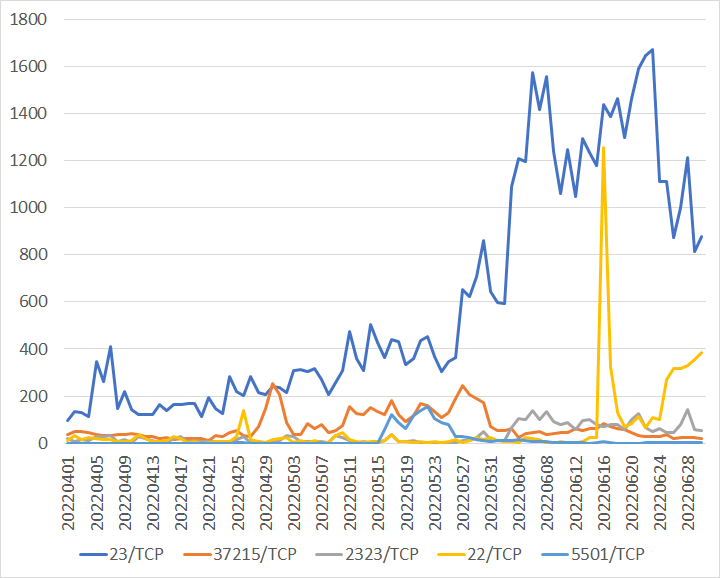
The top 5 ports for the number of packets with Mirai-type characteristics whose source region is Japan were 23/TCP, 37215/TCP, 2323/TCP, 22/TCP, and 5501/TCP. The following figures are based on the ranking: Figure 1 simply shows the changes in the number of packets of the top 5 ports whose source region is Japan, while Figure 2 only shows those with Mirai-type characteristics.
 |
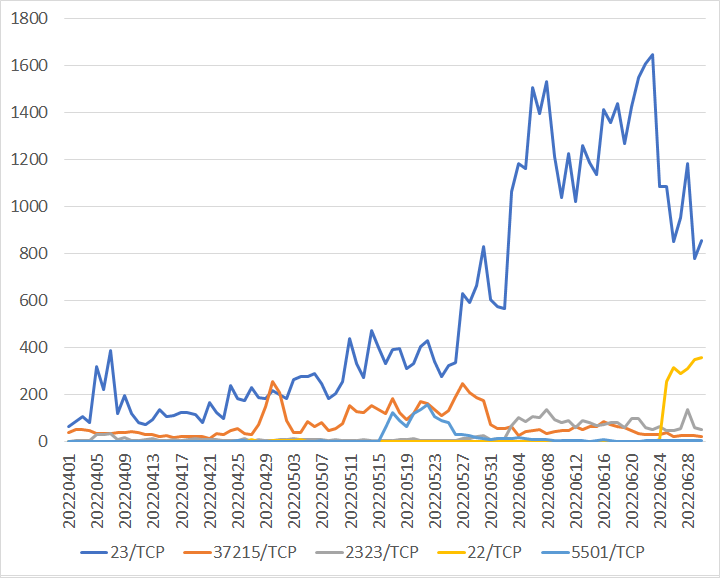 |
| Figure 1: Packets of the top 5 ports whose source region is Japan (All) | Figure 2: Packets of the top 5 ports whose source region is Japan (Mirai-type) |
Although the two graphs above appear to show almost similar trends, there are some differences, such as the sharp increase in Port 22/TCP on June 16 and the shape of the graph for Port 2323/TCP. The differences in the number of total packets are shown in Table 1.
Table 1: Comparison of the number of Mirai-type packets whose source region is Japan and the number of total packets
| 23/TCP | 37215/TCP | 2323/TCP | 22/TCP | 5501/TCP | |
|---|---|---|---|---|---|
| ALL | 54555 | 6554 | 3180 | 5351 | 1285 |
| Mirai-type | 51468 | 6551 | 2679 | 1906 | 1285 |
| Percentage | 94.34% | 99.97% | 84.25% | 35.75% | 100.00% |
23/TCP, 2323/TCP, and 37215/TCP matched over 80% between ALL and Mirai-type packets, and 5501/TCP matched 100%. However, Port 22/TCP matched only less than 40%, which is quite different from the other 4 ports. This is because packets to Port 22/TCP, which has Mirai-type characteristics, have been observed since June 25. An increase in packets for 5501/TCP was also observed. As mentioned above, targeting various protocols by changing port numbers was observed during the quarter.
Comparison of the observation trends in Japan and overseas
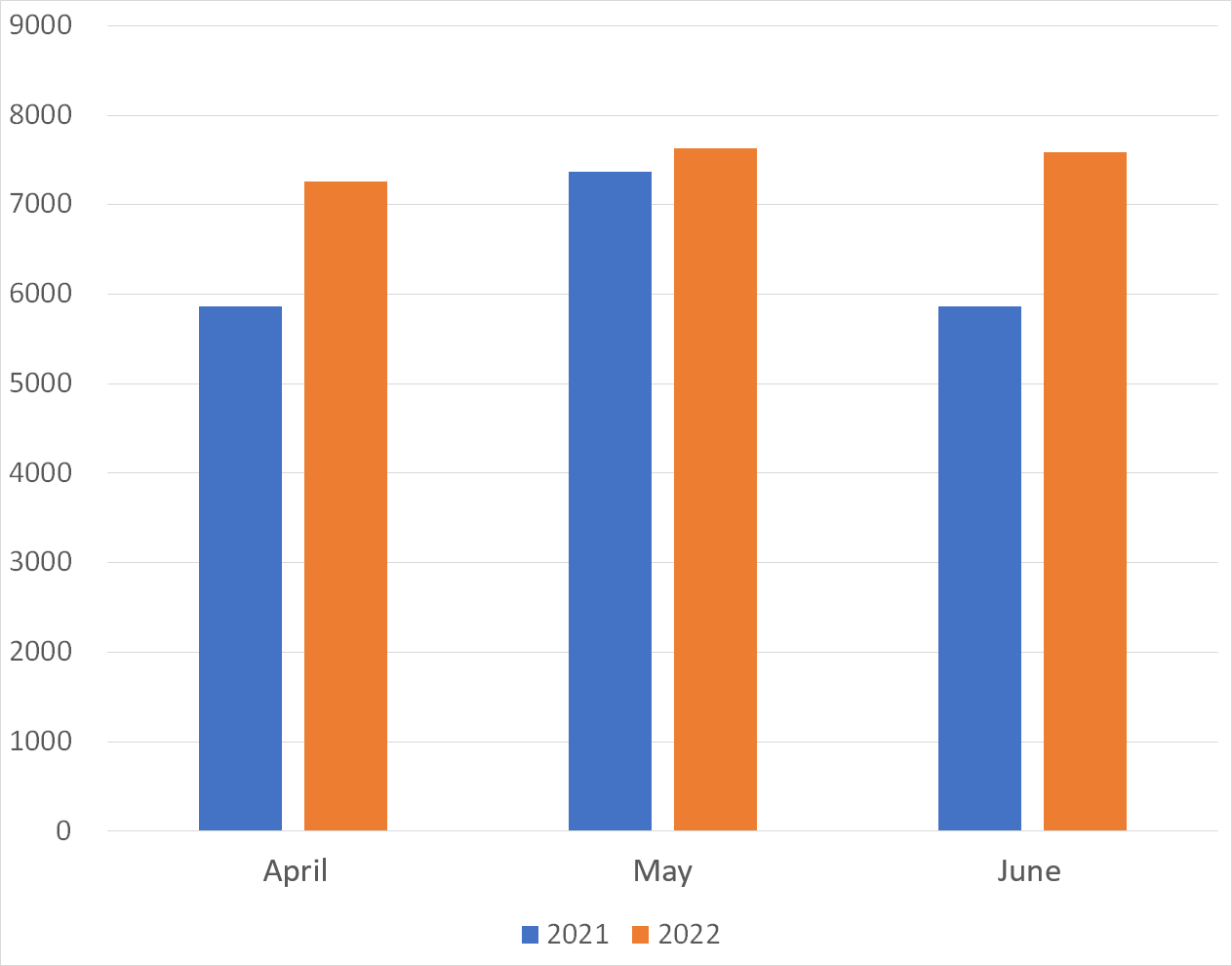
Figures 3 and 4 show a monthly comparison of the average number of packets received per day by each sensor in Japan and overseas. More packets were observed by overseas sensors than those in Japan. More packets were observed in any month than in the same month in 2021 both by sensors in Japan and overseas.
 |
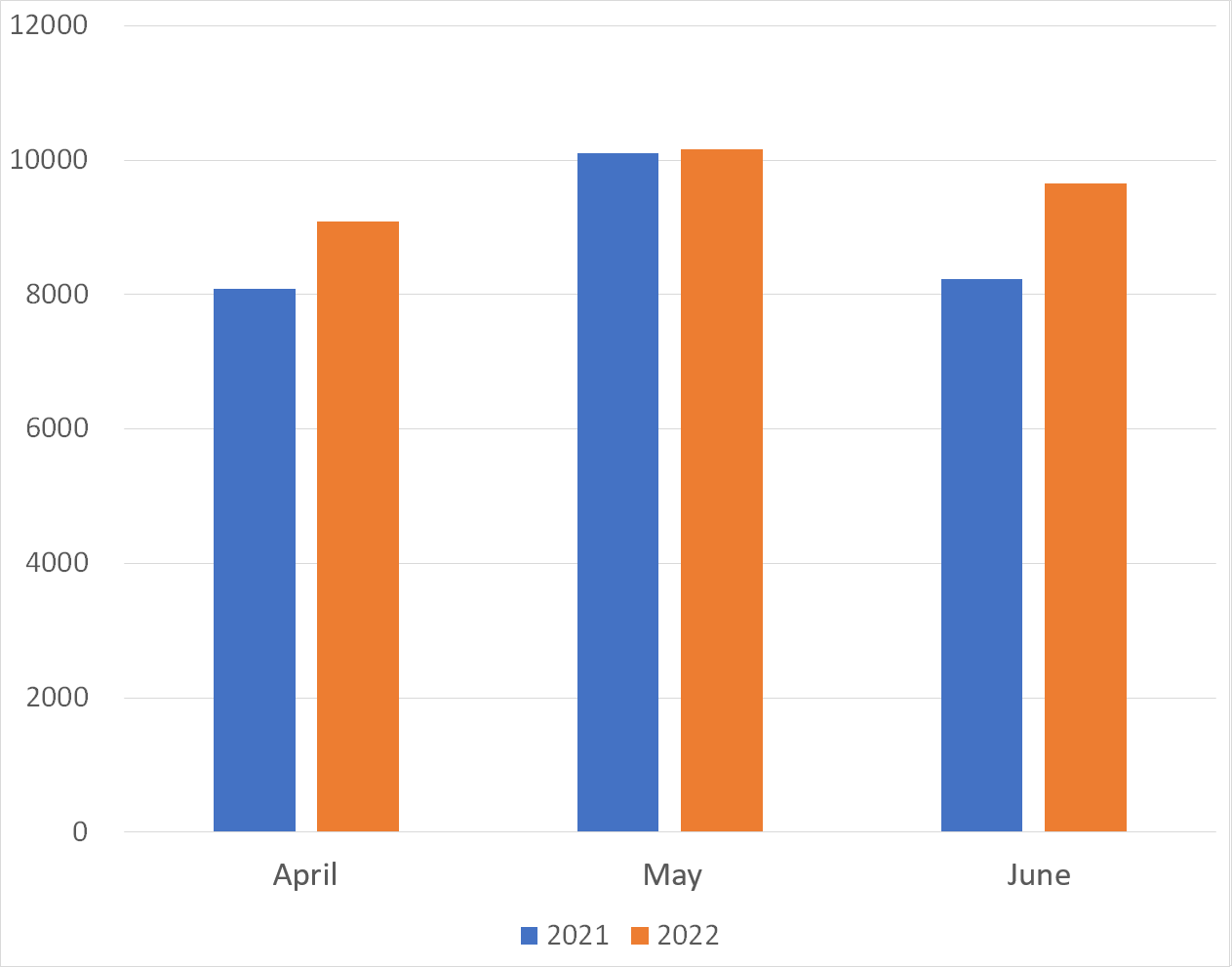 |
| Figure 3: Average number of packets to domestic sensors | Figure 4: Average number of packets to overseas sensors |
Comparison of monitoring trends by sensor
A global IP address is assigned to each TSUBAME sensor. Table 2 shows the top 10 ports of each sensor which received packets the most. Many sensors observe the packets for 23/TCP the most, and 6379/TCP is also in the top 10 on many sensors. In addition, packets for 5555/TCP, which is used by Android’s ADB, were observed on all sensors. Although the order is different between the domestic and international sensors, the combinations were not different significantly. This suggests that these protocols are being scanned in a wide range of networks.
Table 2: Comparison of top 10 packets by domestic and overseas sensors
| #1 | #2 | #3 | #4 | #5 | #6 | #7 | #8 | #9 | #10 | |
| Domestic sensor1 | 23/TCP | 6379/TCP | 22/TCP | 80/TCP | 445/TCP | 5555/TCP | 81/TCP | 3389/TCP | 443/TCP | 1433/TCP |
| Domestic sensor2 | 23/TCP | 6379/TCP | 22/TCP | 80/TCP | 5555/TCP | 445/TCP | ICMP | 443/TCP | 81/TCP | 3389/TCP |
| Domestic sensor3 | 23/TCP | 6379/TCP | 22/TCP | 80/TCP | 445/TCP | 5555/TCP | 37215/TCP | 3389/TCP | 443/TCP | 81/TCP |
| Overseas sensor1 | 23/TCP | 5555/TCP | 22/TCP | 80/TCP | 445/TCP | ICMP | 3389/TCP | 443/TCP | 5060/UDP | 81/TCP |
| Overseas sensor2 | 23/TCP | 6379/TCP | ICMP | 22/TCP | 445/TCP | 7547/TCP | 8291/UDP | 5555/TCP | 80/TCP | 5060/UDP |
| Overseas sensor3 | 445/TCP | 23/TCP | 139/TCP | ICMP | 6379/TCP | 22/TCP | 5555/TCP | 80/TCP | 443/TCP | 5060/UDP |
In Closing
Monitoring at multiple points makes it possible to see whether some trends are unique to a particular network. Although we have not published any special alerts as an extra issue or other information this quarter, it is important to note that the security camera recording devices discussed in this article are the source of the Mirai-type packets. We will continue to publish blog articles as the Internet Threat Monitoring Quarterly Report becomes available every quarter. We will also publish an extra issue when we observe any unusual change. Your feedback on this series is much appreciated. Please use the below comment form to let us know which topic you would like us to introduce or discuss further. Thank you for reading.
Keisuke Shikano (Translated by Takumi Nakano)

