TSUBAME Report Overflow (Oct-Dec 2025)
This TSUBAME Report Overflow series discuss monitoring trends of overseas TSUBAME sensors and other activities which the Internet Threat Monitoring Quarterly Reports do not include. This article covers the monitoring results for the period October to December 2025.
Suspicious Packets Originating from DVR/NVR Devices
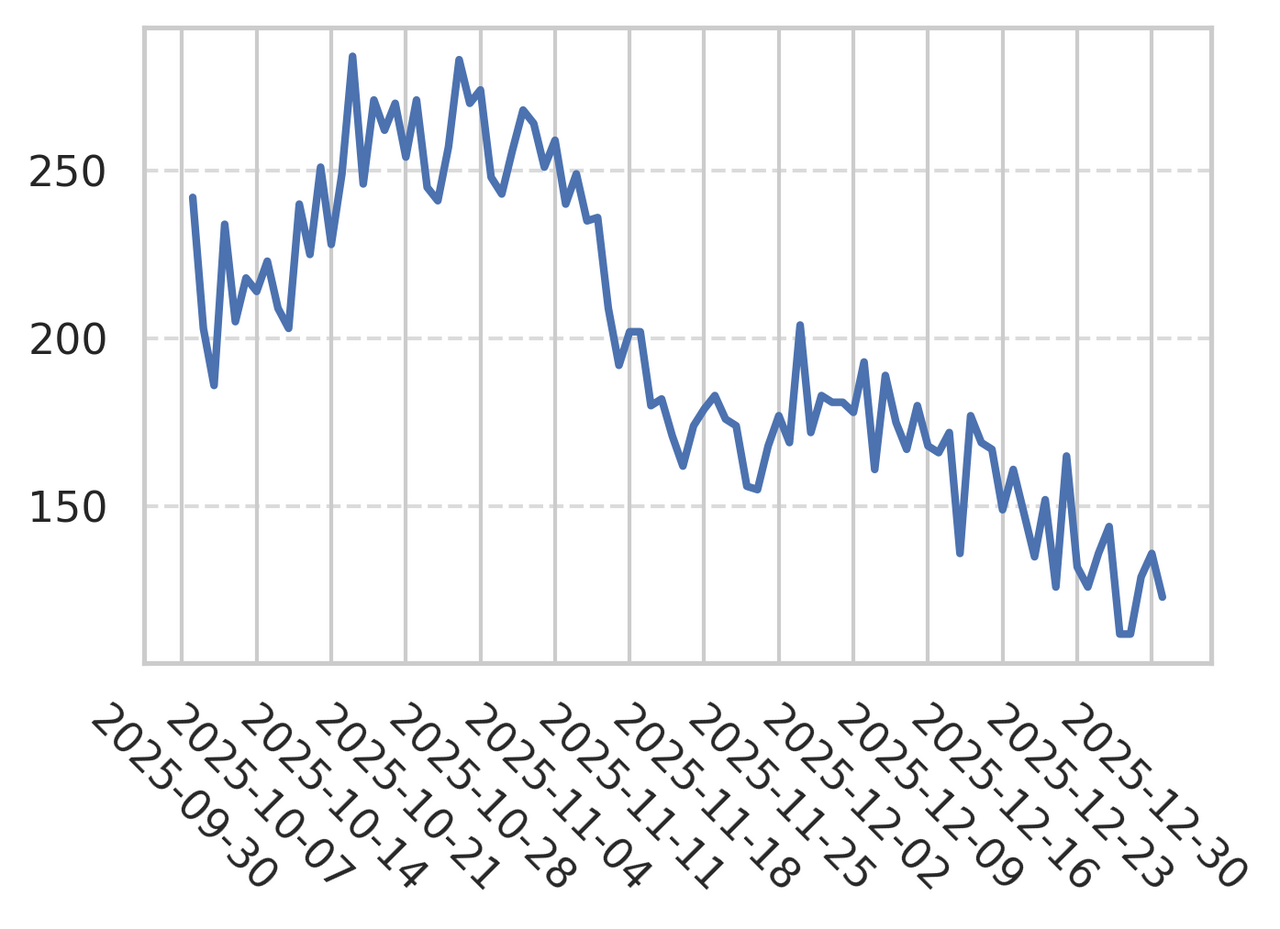
A review of the number of hosts in Japan sending traffic to Telnet (23/TCP) shows a temporary spike in October, followed by a downward trend beginning around November 7 (Figure 1).
|
| Figure 1: Trend in the number of source hosts in Japan sending packets to 23/TCP |
However, a closer look at the sources indicates that many of these connections appear to originate from specific groups of DVR/NVR devices. On some days, these devices accounted for roughly 80% of the total, suggesting that a considerable number of such devices are still actively communicating with external networks. Below are examples of login screens observed from these device groups (Figures 2–5).
|
| Figure 2: Example of a device likely to be a DVR/NVR product |
|
| Figure 3: Example of a device likely to be a DVR/NVR product (2) |

|
| Figure 4: Example of a device likely to be a DVR/NVR product (3) |

|
| Figure 5: Example of a device likely to be a DVR/NVR product (4) |
Some of these interfaces display outdated copyright years (e.g., 2014), which suggests that firmware may not have been updated for a long time. Devices in this state may still contain known vulnerabilities, making them more susceptible to attacks from the Internet. If you are using similar devices, we recommend checking whether they fall into this category and taking this opportunity to ensure that firmware updates are properly applied.
Comparison of the observation trends in Japan and overseas
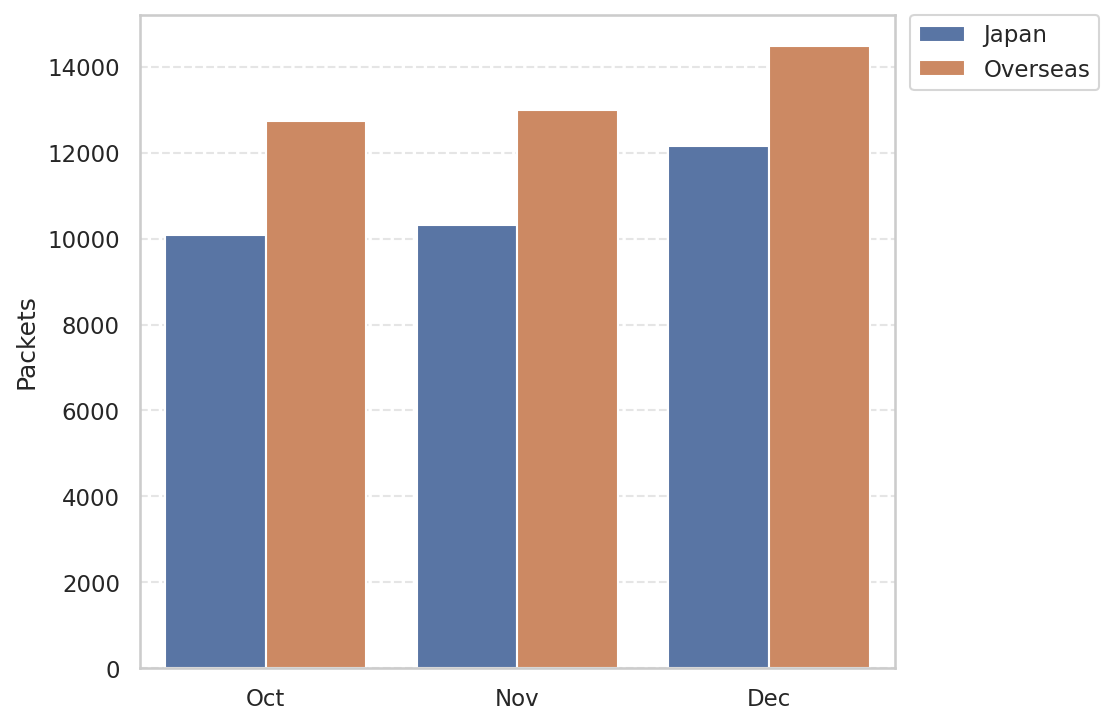
Figure 6 is a monthly comparison of the average number of packets received in Japan and overseas. Overseas sensors received more packets than those in Japan. Additionally, a gradual upward trend was observed from October onward across both domestic and overseas sensors.
|
| Figure 6: Monthly comparison of the average number of packets received in Japan and overseas |
Comparison of monitoring trends by sensor
Each sensor is assigned a single global IP address. To examine differences in monitoring trends among sensors in Japan, North America, Europe, and other regions, Table 1 summarizes the top 10 destination ports that received packets. Although the rankings vary by sensor, ports such as 22/TCP, 23/TCP, 80/TCP, 443/TCP, and 8080/TCP were observed by almost all sensors. This suggests that scanning activity targeting these protocols is being conducted across a wide range of networks.
Table 1: Comparison of top 10 packets by domestic and overseas sensors
| Japan #1 | Japan #2 | North America #1 | North America #2 | Europe #1 | Europe #2 | Other regions #1 | Other regions #2 | |
|---|---|---|---|---|---|---|---|---|
| #1 | 23/TCP | 23/TCP | 443/TCP | 23/TCP | 23/TCP | 23/TCP | 443/TCP | 23/TCP |
| #2 | 80/TCP | ICMP | ICMP | 22/TCP | 8080/TCP | 8080/TCP | 23/TCP | 443/TCP |
| #3 | 443/TCP | 80/TCP | 23/TCP | 443/TCP | 443/TCP | 443/TCP | 8728/TCP | 8728/TCP |
| #4 | 8080/TCP | 443/TCP | 80/TCP | 8728/TCP | 3389/TCP | ICMP | ICMP | 80/TCP |
| #5 | 22/TCP | 22/TCP | 8728/TCP | 3389/TCP | 80/TCP | 80/TCP | 80/TCP | ICMP |
| #6 | ICMP | 8443/TCP | 22/TCP | 80/TCP | 22/TCP | 3389/TCP | 22/TCP | 22/TCP |
| #7 | 8728/TCP | 8080/TCP | 3389/TCP | ICMP | ICMP | 22/TCP | 3389/TCP | 3389/TCP |
| #8 | 3389/TCP | 8728/TCP | 8080/TCP | 8080/TCP | 8728/TCP | 445/TCP | 8080/TCP | 8080/TCP |
| #9 | 81/TCP | 3389/TCP | 8443/TCP | 8443/TCP | 445/TCP | 8728/TCP | 8443/TCP | 8443/TCP |
| #10 | 5555/TCP | 5555/TCP | 6379/TCP | 2222/TCP | 1433/TCP | 8443/TCP | 2222/TCP | 2222/TCP |
In closing
Monitoring at multiple locations enables us to determine if certain changes are occurring only in a particular network. Although we have not published any special alerts as an extra issue or other information this quarter, it is important to pay attention to scanners. We will continue to publish blog articles as the Internet Threat Monitoring Quarterly Report becomes available every quarter. We will also publish an extra issue when we observe any unusual change. Your feedback on this series is much appreciated. Please use the comment form below to let us know which topic you would like us to introduce or discuss further. Thank you for reading.
Keisuke Shikano
(Translated by Takumi Nakano)

