TSUBAME Report Overflow (Jul-Sep 2025)
This TSUBAME Report Overflow series discusses monitoring trends observed by overseas TSUBAME sensors, as well as other activities that are not included in the Internet Threat Monitoring Quarterly Reports. This article covers the monitoring results from July to September 2025.
Suspicious packets from domestic NVR products
In the main issue of the Internet Threat Monitoring Report, we presented observations of packets originating from TP-Link routers suspected to be infected with malware among nodes with source IP addresses in Japan. However, our honeypots have TSUBAME has also observed packets transmitted from devices manufactured by vendors other than TP-Link. For some source IP addresses, multiple open ports were confirmed. In such cases, it is assumed that port forwarding is configured on the router deployed at the IP address, enabling multiple devices to provide services behind a single global IP address. While this type of configuration is not uncommon, it is difficult to identify which specific device has been compromised based solely on external observations. In this article, we introduce a particularly noteworthy case observed among IP addresses where multiple devices are operating in combination. The characteristics observed for each IP address are summarized below:
- A login page for an NVR product was accessible
- An administration interface for an enterprise router manufactured by a Japanese company was accessible.
- A login page for an SDN controller was accessible
One notable characteristic of this case is that the Web UIs of these devices were listening on the same port numbers, even though they were hosted on different IP addresses. In addition, the administration interface of the domestically manufactured routers contained a character string presumed to be an abbreviation of a prefecture name, suggesting that the systems may be deployed across multiple regions. Based on these findings, it is possible that a system department or the SI/NIer responsible for deployment provisioned these systems using identical configurations. Given that suspicious packets have been observed, there is a high likelihood that one or more of the devices have been compromised. Although we are currently attempting to contact the users operating these systems, we have not yet been successful.
Comparison of the observation trends in Japan and overseas
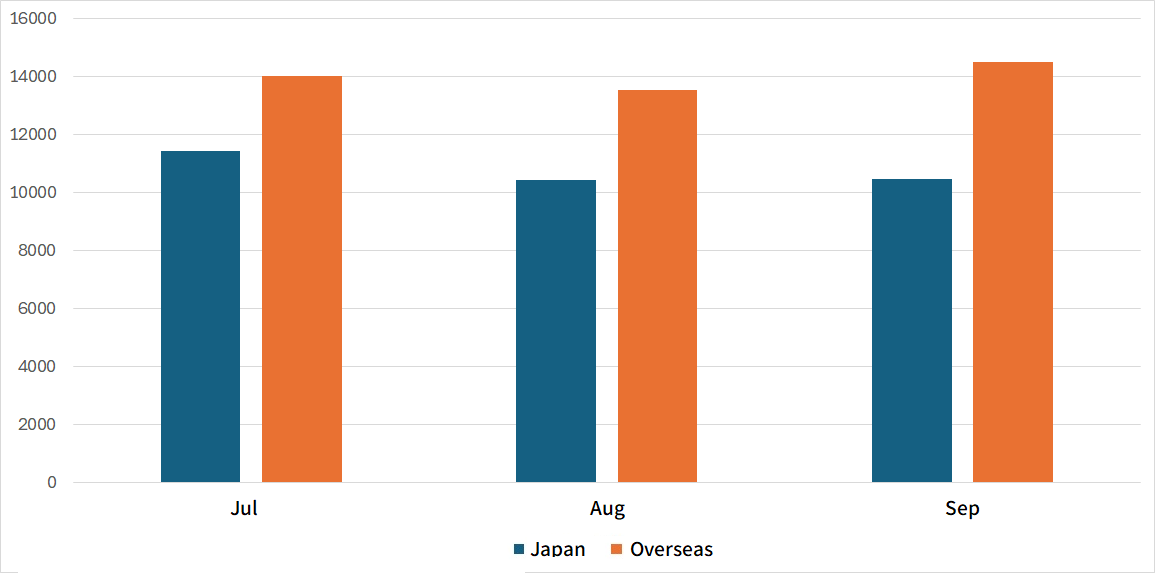
Figure 1 is a monthly comparison of the average number of packets received in Japan and overseas. Overseas sensors received more packets than those in Japan. For domestic sensors, the number of packets peaked in July and then gradually decreased month by month. In contrast, packets from overseas sensors declined once through August, but increased again in September.
|
| Figure 1: Monthly comparison of the average number of packets received in Japan and overseas |
Comparison of monitoring trends by sensor
Each sensor is assigned a single global IP address. To examine differences in monitoring trends among sensors in Japan, North America, Europe, and other regions, Table 1 summarizes the top 10 destination ports that received packets. Although the rankings vary by sensor, ports such as 22/TCP, 23/TCP, 80/TCP, 443/TCP, and 8080/TCP were observed by almost all sensors. This suggests that scanning activity targeting these protocols is being conducted across a wide range of networks.
Table 1: Comparison of top 10 packets by domestic and overseas sensors
| Japan #1 | Japan #2 | North America #1 | North America #2 | Europe #1 | Europe #2 | Other regions #1 | Other regions #2 | |
|---|---|---|---|---|---|---|---|---|
| #1 | <23/TCP | 23/TCP | 80/TCP | 23/TCP | 23/TCP | ICMP | ICMP | 22/TCP |
| #2 | 80/TCP | 80/TCP | ICMP | 22/TCP | 443/TCP | 443/TCP | 23/TCP | 23/TCP |
| #3 | 3389/TCP | 443/TCP | 443/TCP | 3389/TCP | 443/TCP | 80/TCP | 22/TCP | ICMP |
| #4 | 22/TCP | 8080/TCP | 23/TCP | 80/TCP | 80/TCP | 23/TCP | 80/TCP | 80/TCP |
| #5 | ICMP | 8888/TCP | 22/TCP | 443/TCP | 22/TCP | 22/TCP | 443/TCP | 443/TCP |
| #6 | 8080/TCP | 22/TCP | 8728/TCP | 8728/TCP | 8728/TCP | 8728/TCP | 8728/TCP | 8728/TCP |
| #7 | 443/TCP | 3389/TCP | 3389/TCP | 8080/TCP | 3389/TCP | 3389/TCP | 3389/TCP | 3389/TCP |
| #8 | 5555/TCP | ICMP | 8080/TCP | ICMP | 8080/TCP | 8080/TCP | 8080/TCP | 8080/TCP |
| #9 | 34567/TCP | 8728/TCP | 8443/TCP | 445/TCP | 8443/TCP | 8443/TCP | 6379/TCP | 8443/TCP |
| #10 | 60000/TCP | 5555/TCP | 6379/TCP | 8081/TCP | 6379/TCP | 6379/TCP | 2222/TCP | 2222/TCP |
In closing
Monitoring at multiple locations enables us to determine whether certain changes are occurring only within a specific network. Although we did not publish any special alerts or extra issues this quarter, it remains important to pay close attention to scanning activity. We will continue to publish blog articles as part of the Internet Threat Monitoring Quarterly Report each quarter, and we will also release an extra issue if we observe any unusual changes. We greatly appreciate your feedback on this series. Please use the comment form below to let us know which topics you would like us to introduce or discuss further. Thank you for reading.
Keisuke Shikano
(Translated by Takumi Nakano)

