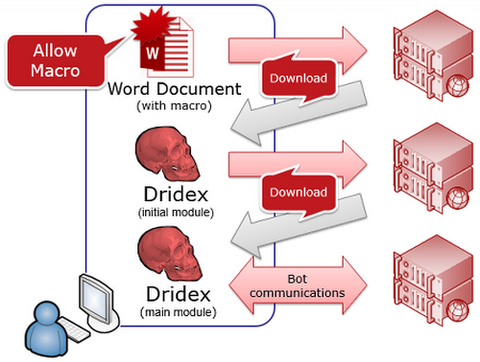
NOTE: This article, originally published on 13 February, 2015, was updated as of 12 May, 2015 (See below). Hello all, this is You Nakatsuru (“TSURU”) from Analysis Center again. Today, I would like to describe a new UAC bypass method that has been used by the Dridex malware since December, 2014. Introduction Dridex is a banking trojan, which is a bot that communicates with a CC server through HTTP. Most...
List of “JPCERT/CC”
-
-
Happy New Year 2015 to everyone! I am Toru Yamauchi, Research Director of JPCERT/CC. JPCERT/CC has been contributing to the CSIRT community in Africa in order to enhance the global cybersecurity activity. In the rapid ICT development in Africa, it is getting more important for them to accelerate human development in cybersecurity area and to establish regional cooperation especially among National CSIRTs. I would like to introduce our recent on-site...
-
Hello and Happy Holiday Season to everybody. Taki again, and today I will write about some experiences in product (software, hardware) vulnerability coordination this year. - Introduction - A lot happened this year and I do not have the time to go through everything, but would like to go over some of the major issues that we handled and for those that are not familiar, provide a very brief overview...
-
Hello, this is Osamu from Global Coordination Division. It’s been 2 years since I posted the last article here. Today, I am going to share our experience at the event organized in Thailand last month. In late October, ThaiCERT, a member of ETDA (Electronic Transactions Development Agency), and JPCERT/CC organized an event “Malware Analysis Competition 2014 (MAC 2014)” in Bangkok, Thailand. The event consisted of 3 parts: Basic Malware Analysis...
-
Hello, this is Taki and today I would like to write about my trip to Colombo, Sri Lanka from September 30th through October 2nd. I went with Tetsuya to conduct TSUBAME trainings at Sri Lanka CERT|CC and TechCERT, and to give a presentation at Cyber Security Week 2014 - 7th Annual National Conference on Cyber Security. TSUBAME Training for Sri Lanka CERT|CC and TechCERT Unlike our previous TSUBAME trainings in...
-
Hello. This is Masaki from Vulnerability Analysis Team. JPCERT/CC has been active in doing research, developing coding standards and conducting seminars in secure coding since 2007. In the course of our activities, we've collaborated with CSIRTs in Asia-Pacific region such as ThaiCERT, PHCERT, ID-SIRTII/CC, Academic-CERT in Indonesia, VNCERT and CERT-In in providing secure coding training to software developers in each region. Last month, Hiroshi (my teammate and senior vulnerability analyst),...
-
Konnichiwa, this is Kaori at Global Coordination Division. On September 17th, JPCERT/CC and Information-technology Promotion Agency (IPA) of Japan have jointly issued a notice to raise public awareness to refrain from using a single password for multiple online services. On the same day, JPCERT/CC, as our sole initiative, has launched a local campaign to further promote this practice by having the enterprise supporters to directly encourage their users. This password...
-
It's been quite a while. This is Taki again and I will be writing about my experiences at the 26th FIRST Annual Conference in Boston that I attended from June 23 - 27. (Trinity Church - Photo by Hiroshi Kobayashi) This year, I attended the conference with 3 colleagues, Yurie Ito, Koichiro (Sparky) Komiyama and Hiroshi Kobayashi. Having attended the conference on a few occasions in the past, it was...
-
Hi! I’m Takuho Mitsunaga from Watch and Warning Group. I am pleased to announce that JPCERT/CC has just released a report "Investigation Report Regarding Security Issues of Web Applications Using HTML5 (English version)." As mentioned in the previous posts - JPCERT/CC at “CODE BLUE” and Presenting HTML5 security at OWASP AppSec APAC 2014, through publishing a report (Japanese version), we have worked to point out the issues and raise awareness...
-
I am Toru Yamauchi, Research Director of JPCERT/CC. JPCERT/CC has been contributing to CSIRT community in Africa since 2010 in order to enhance the global cybersecurity activity. In the rapid ICT development in Africa, it is getting important for African community to accelerate human resource development of cybersecurity and to establish the regional cooperation especially among National CSIRTs. I would like to introduce our recent on-site training program in Djibouti...