JPCERT/CC released the latest version (v1.6) of LogonTracer, a tool to support event log analysis. Previously, LogonTracer could not investigate multiple incidents simultaneously, but this update adds support for managing multiple logs. In addition, Sigma can now be used to investigate the presence of suspicious logs in the event log. This article introduces these updates. For other updated items, please refer to the following release: https://github.com/JPCERTCC/LogonTracer/releases/tag/v1.6.0 Log Management Feature When...
List of “朝長 秀誠 (Shusei Tomonaga)”
-
-
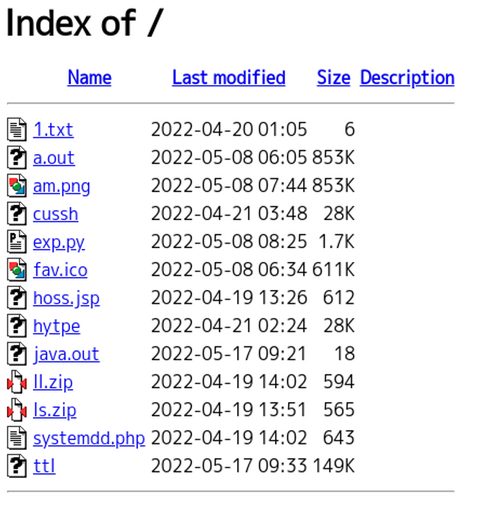
Around May 2022, JPCERT/CC confirmed an attack activity against Japanese organizations that exploited F5 BIG-IP vulnerability (CVE-2022-1388). The targeted organizations have confirmed that data in BIG-IP has been compromised. We consider that this attack is related to the activities by BlackTech attack group. This blog article describes the attack activities that exploit this BIG-IP vulnerability. Attack code that exploits the BIG-IP vulnerability Below is a part of the attack code...
-
JPCERT/CC is continuously investigating the activities by Lazarus. In ...
-
Some types of malware use DGA, obfuscate destination information, or c...
-
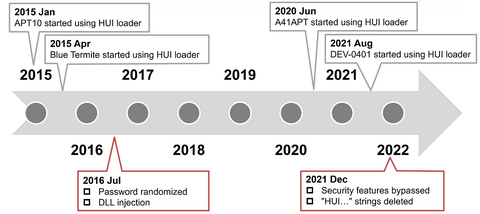
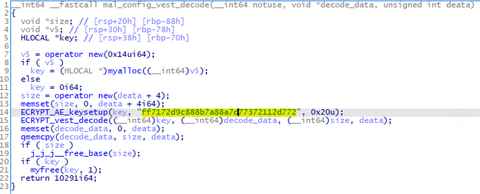
To conceal malware’s features, attackers sometimes encode the malware and decode it only when they execute it. In such cases, the encoded malware is loaded and executed by a program called loader. In this way, an attacker can split the malware into a loader and encoded malware. Minimizing the loader’s features and hiding important features of the malware make detection on infected hosts more difficult. Among such loaders, this article...
-
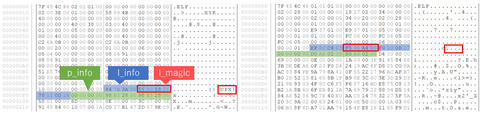
Malware targeting Windows OS (PE format) has a variety of obfuscation and packing techniques in place so that they complicate the code analysis processes. On the other hand, there are only a few types of packing techniques for Linux-targeting malware (ELF format), and it is mainly UPX-based. This blog article explains the details of Anti-UPX Unpacking technique, which is often applied to Linux-targeting malware. Malware with Anti-UPX Unpacking Technique The...
-
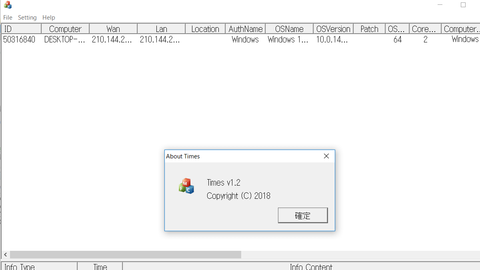
An attack group BlackTech has been actively conducting attacks against Japanese organisations since 2018. Although it is not as prominent as before, JPCERT/CC is still seeing some cases as of now. This article introduces the details of the malware Gh0stTimes, which is used by this group. Gh0stTimes overview Gh0stTimes is customised based on Gh0st RAT and has been used in some attack cases since 2020. Figure 1 shows the comparison...
-
Volatility 3 had long been a beta version, but finally its v.1.0.0 was released in February 2021. Since Volatility 2 is no longer supported [1], analysts who used Volatility 2 for memory image forensics should be using Volatility 3 already. In this blog post, I introduce a tip for Volatility 3: how to use Volatility 3 offline. This instruction focuses on analyzing Windows OS memory image. What is the problem...
-
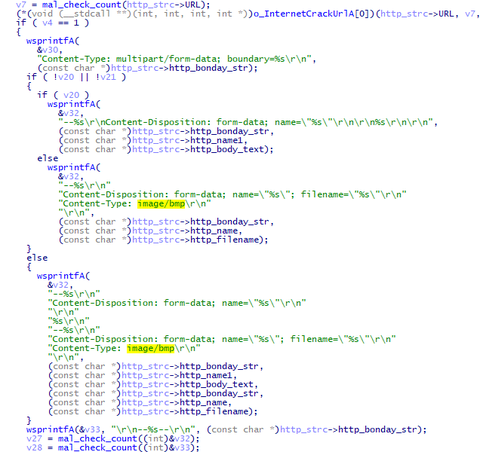
The attack group Lazarus (also known as Hidden Cobra) conducts various attack operations. This article introduces malware (VSingle and ValeforBeta) and tools used in attacks against Japanese organisations. VSingle overview VSingle is a HTTP bot which executes arbitrary code from a remote network. It also downloads and executes plugins. Once launched, this malware runs Explorer and executes its main code through DLL injection. (Some samples do not perform DLL injection.)...
-
Lazarus (also known as Hidden Cobra) is known to use various kinds of malware in its attack operations, and we have introduced some of them in our past articles. In this article, we present two more; Torisma and LCPDot. Torisma overview Torisma downloads and executes modules from external servers, and its infection spreads via malicious Word files [1]. Torisma samples that JPCERT/CC has analysed are DLL files and executed as...