Bug in Malware “TSCookie” - Fails to Read Configuration - (Update)
Our past article has presented a bug in malware “TSCookie”, which is reportedly used by BlackTech attack group. This article is to update the features of the malware.
Even after we published the blog article in October 2018, the adversary had continued using the malware as it was. Just in May 2019, we confirmed that the malware had its bug fixed and was used in some attack cases.
Details of the fix
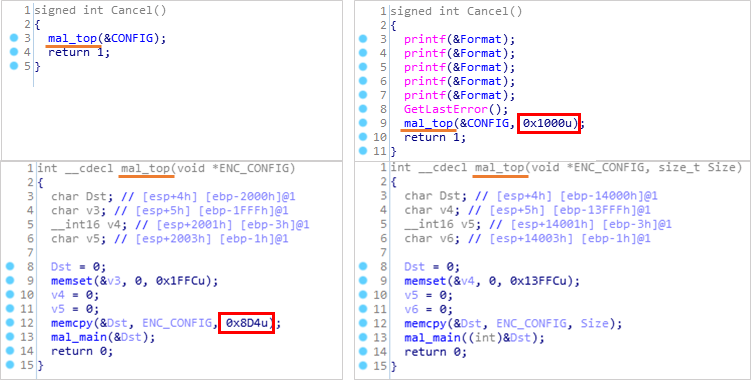
The malware copies its configuration to the memory. In the previous version, the data size to be copied was incorrectly set, which resulted in the configuration not displayed properly (see the article for more details). In the updated version, the data size is set to 0x1000 instead of 0x8D4.
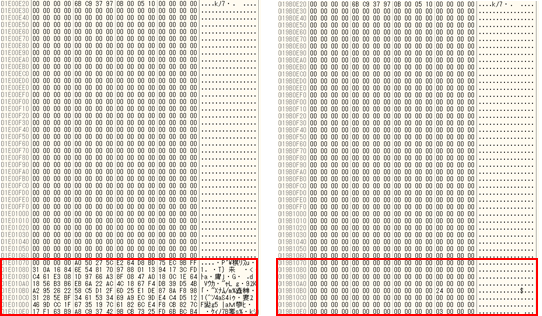
This update enables TSCookie to decode the configuration correctly. Fig 2 is the comparison of decoded configuration. This update has also fixed the issue where the malware fails to reconnect to a C&C server for a few days.
In closing
As we pointed out before, it is likely that adversaries also follow publications and blogs from security vendors, etc. We assume that the adversary recognised the bug on our blog and fixed the issue accordingly. If we see any updates on the malware, we will introduce them here.
Hash values of the samples described in the article are listed in Appendix A, along with C&C servers in Appendix B. Please make sure that none of your devices is accessing these hosts.
Thank you for reading.
Shusei Tomonaga
(Translated by Yukako Uchida)
Appendix A: Hash value of the samples
Malware with the bug
- 96723797870a5531abec4e99fa84548837e9022e9f22074cf99973ab7df2a2e7
Updated malware
- 1ec19677d1e48e4f6ff5f9fe7808b13964059e2ffd48ece19f7305d78e04ec4a
- c2c062ff84a18ad02e92dea0d6e12cafa66ff167ea8d02663fc9aae44de7f4e0
Appendix B: List of C&C servers
- www.google.com.dns-report.com
- microsoft.com.appstore.dynamicdns.co.uk
- cartview.viamisoftware.com

