Greetings. This is Aki Hitotsuyanagi from ICS Security Response Group. Today, I would like to introduce to you our new document, “Cyber Security First Step for Introducing IIoT to the Factory -Security Guide for Businesses Implementing IIoT-“.The original Japanese version of this document was released August 2018 and has been receiving favorable reviews. IIoT, or Industrial Internet of Things refers to use of IoT in industrial sectors. For example, using...
-
-
xin chào! (“Hello” in Vietnamese) This is Katsuhiro Mori from Cyber Me...
-
Following the JSAC2019 Part 1, this article will provide overview of the latter half of the conference. We also uploaded the photos from the conference on Flickr. “Sextortion Spam Demanding Cryptocurrency” by Chiaki Onuma (Kaspersky) Presentation material (Japanese) Sextortion spam is a campaign distributing spam emails in which adversaries aim to extort money (e.g. bitcoin) by threatening recipients by means of sexual contents. Ms. Onuma shared the outcome of her...
-
JPCERT/CC organised Japan Security Analyst Conference 2019 (JSAC2019) on 18 January 2019 in Ochanomizu, Tokyo. This conference targets front-line security analysts who deal with cyber incidents on a daily basis, with an aim to create a venue for sharing technical information which helps them better handle ever-evolving cyber attacks. This is the second run of the event following the first one in 2018, and 291 participants attended. In this event,...
-
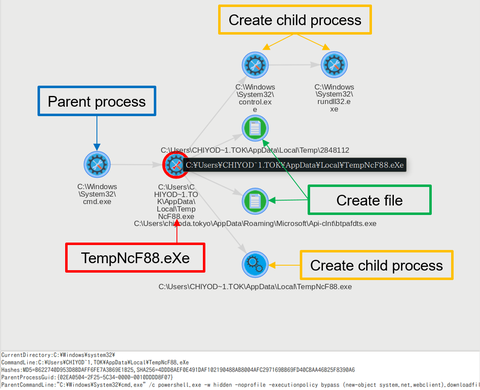
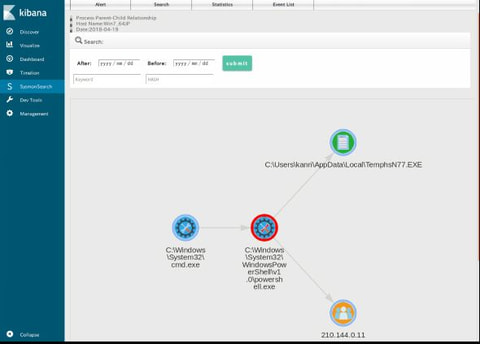
In a past article in September 2018, we introduced a Sysmon log analysis tool "SysmonSearch" and its functions. Today, we will demonstrate how this tool can be used for incident investigation by showing some examples. To install SysmonSearch, please see the following page: JPCERTCC GitHub · SysmonSearch Wiki https://github.com/JPCERTCC/SysmonSearch/wiki The case study was conducted in the following environment: Sysmon 7.0.1 ElasticSearch 6.2.2 Kibana 6.2.2 Winlogbeat 6.2.2 Browser: Firefox Example of...
-
Hi, this is Katsuhiro Mori from Cyber Metrics Line, Global Coordinatio...
-
Hello, I am Katsuhiro Mori from Cyber Metrics Line, Global Coordination Division. JPCERT/CC released ”Mejiro” (Internet risk visualisation service) English website in August 2018. This web service collects publicly available risk data on risk factors existing on the Internet and provides index for each economy. To promote the use of this tool service and cyber space clean-up activities, I went to Mongolia and Indonesia recently. What is Mongolia like? When...
-
In a previous article we have introduced malware ‘TSCookie’, which is assumedly used by an attacker group BlackTech. We have been observing continuous attack activities using the malware until now. In the investigation of an attack observed around August 2018, we have confirmed that there was an update in the malware. There are two points meriting attention in this update: Communication with CC server Decoding configuration information This article will...
-
Greetings from JPCERT/CC! Thank you for visiting JPCERT/CC blog. We are happy to announce that we now have a new blog site "JPCERT/CC Eyes". The new URL is https://blogs.jpcert.or.jp/en/. The previous articles published on the existing platform have been tranferred to this new site. We will continue to provide our technical insights and latest cyber security trends on this site with the new fresh look. Thank you and stay tuned!...
-
In recent sophisticated cyber attacks, it is common to observe lateral movement, where a malware- infected device is used as a stepping stone and further compromise other devices in the network. In order to investigate the compromised devices, it is necessary to retain detailed logs of the applications that run on the device on a daily basis. One of the well-known tools for this purpose is Sysmon [1] from Microsoft,...