Hello all, my name is Shinichi Horata working at Watch and Warning Group. It’s my first time posting here. It’s already been quite a while ago, but last year I went to Mongolia for the first time in my life. The purpose was to attend MNSEC 2015 (Conference website: Mongolian only), a Mongolian local cyber security conference hosted by MNCERT/CC (Organisation website: Mongolian only) on 29-30 September 2015, where I...
-
-
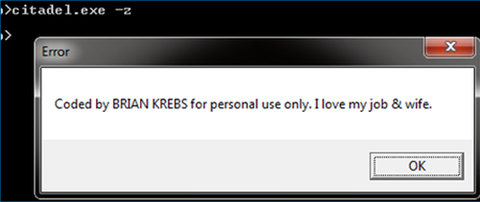
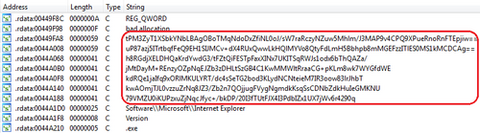
Hello again, this is You ‘Tsuru’ Nakatsuru from Analysis Center. It has been just about two years since I delivered a talk “Fight Against Citadel in Japan” at CODE BLUE 2013 (an international security conference in Tokyo) about the situation on banking trojans observed in Japan at that time and detailed analysis results on Citadel (See my blog entry here). For the presentation material and audio archive, please see Reference...
-
Hello again, this is Shusei Tomonaga from the Analysis Center. In Windows OS, various commands (hereafter “Windows commands”) are installed by default. However, what is actually used by general users is just a small part of it. On the other hand, JPCERT/CC has observed that attackers intruding into a network also use Windows commands in order to collect information and/or to spread malware infection within the network. What is worth...
-
Hi, this is You 'Tsuru' Nakatsuru again from Analysis Center. This past summer, I joined the “Security Camp 2015” in Japan as a trainer for a malware analysis training course, which was held for students aged 22 and under living in Japan, with the aim of discovering top, young talents. This blog entry is to introduce the malware analysis training materials which I used at Security Camp 2015 as below....
-
Hello, this is You ‘Tsuru’ Nakatsuru at Analysis Center. As introduced in the previous blog post, my colleagues presented on the attacks arising in Japan at CODE BLUE 2015, entitled “Revealing the Attack Operations Targeting Japan”. In this entry, I will introduce the details of an IDAPython script “emdivi_string_decryptor.py”, which JPCERT/CC developed to analyse Emdivi, a remote control malware. The script was also introduced in our presentation at CODE BLUE...
-
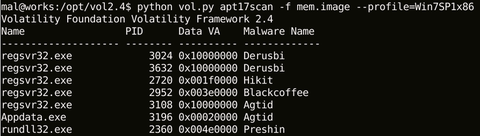
Hello again – this is Shusei Tomonaga from Analysis Center. This blog entry is to introduce “apt17scan.py” created by JPCERT/CC to detect certain malware used in targeted attacks, and to extract its configuration information. It is a plugin for the Volatility Framework (hereinafter “Volatility”), a memory forensics tool. My colleague Yuu Nakamura and I had the honour to introduce this at CODE BLUE 2015, an international conference for information security...
-
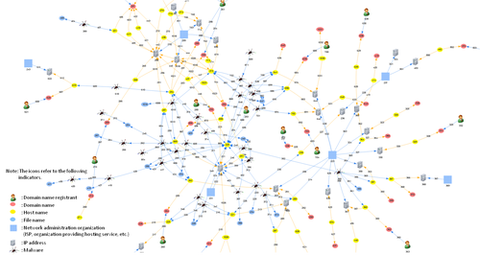
You may well have heard of the May cyber attack in Japan against the Japan Pension Service – a high-profile case seen in the first half of this year, where 1.25 million cases of personal data was exposed. According to the Japan Pension Service, the data leaked included names and ID numbers, and for some cases, dates of birth and home addresses. The official reports(1) say that the massive leak...
-
Hello again, it’s Yuka at the Global Coordination Division. Following my recent trip to Malaysia to join APCERT Annual General Meeting and Conference 2015, I had my first travel to Europe – and that was to Bucharest, Romania to attend a conference hosted by CERT-RO, the National CSIRT of Romania. They host a conference annually, and this year it was the 5th time for this event, held from 5th -...
-
Hi again, it’s Yuka from Global Coordination Division and also serving as APCERT Secretariat. It’s been a while since I wrote here last time. My entry this time is about the biggest event of APCERT which we just recently attended, the Annual General Meeting (AGM) and Conference 2015 in Kuala Lumpur, Malaysia on 6-10 September. This event, hosted by CyberSecurity Malaysia (MyCERT), marked the 12th annual conference for APCERT. What...
-
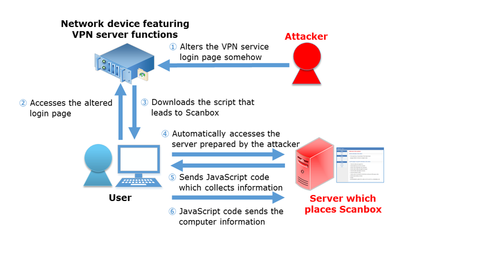
Hi, it’s Shusei Tomonaga again from the Analysis Center. JPCERT/CC has confirmed several attack cases around May 2015, which attempt to steal information of computers leveraging specific network devices featuring VPN server functions. The target of the reconnaissance varies from installed software to keylogs, and it is presumed that the attacker has aimed to steal such information from computers which attempt to login to VPN servers through altered login pages....