JPCERT/CC held JSAC2024 on January 25 and 26, 2024. The purpose of this conference is to raise the knowledge and technical level of security analysts, and we aimed to bring them together in one place where they can share technical knowledge related to incident analysis and response. The conference was held for the seventh time and, unlike last year, returned to a completely offline format. 17 presentations, 3 workshops, and...
List of “JPCERT/CC”
-
-
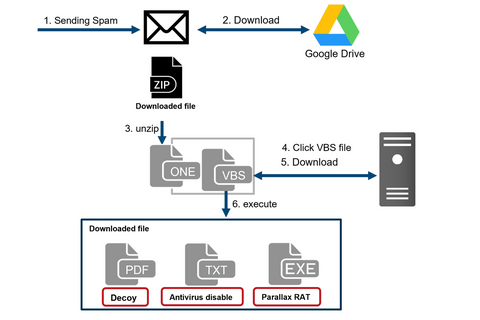
Around February 2023, JPCERT/CC identified an attack that attempted to infect a crypto asset exchanger with the Parallax RAT malware. This attack attempted to infect employees of the crypto asset exchanger with malware by sending spam emails. This article presents the details of this attack.Flow of events leading to Parallax RAT infectionFigure 1 shows the flow of this attack. The identified attack starts with a spam email, which urges the...
-
We continue to introduce the talks at JSAC2023. This third issue covers the workshops on Day 2. Surviving the hurt locker: or How I Learned to Stop Worrying and Love the Bom Speakers: Simon Vestin, Manabu Niseki (LINE) Simon and Manabu explained the SBOM (Software Bill of Materials) and gave a hands-on session on creating a program to generate one. SBOM is a list of software or system components. They...
-
This article reports on JSAC Day 2, following the previous article about Day1. How Do We Fight against Evolving Go Language Malware? Practical Techniques to Increase Analytical Skills Speakers: Tsubasa Kuwabara (FFRI Security Inc.) Slides (English) Tsubasa presented the current situation and problems of Go language malware, which has been increasing in recent years, and explained basic and advanced analysis techniques. He explained that Go malware was easy to write...
-
JPCERT/CC held JSAC2023 on January 25 and 26, 2023. The purpose of this conference is to raise the knowledge and technical level of security analysts in Japan, and we aimed to bring them together in one place where they can share technical knowledge related to incident analysis and response. This year was the sixth time the conference was held, and 12 presentations, 2 workshops, and 7 lightning talks were presented...
-
JPCERT/CC held JSAC2022 online on January 27, 2022. The purpose of this conference is to raise the knowledge and technical level of security analysts in Japan, and we aimed to bring them together in one place where they can share technical knowledge related to incident analysis and response. This year was the fifth time the conference was held. 9 presentations and 2 workshops, selected from 18 CFP and CFW submissions,...
-
This blog post focuses on the Day 2 of JSAC2022, following the previous report on the Day 1.An Introduction to macOS Forensics with Open Source SoftwareSpeaker: Minoru Kobayashi (Internet Initiative Japan Inc.)SlidesVideoMinoru provided the basic knowledge of macOS forensics, and its analysis methods using mac_apt, followed by hands-on training on macOS forensics.He mentioned that when it comes to forensics, information is acquired and analysed at the same priority as macOS...
-
JPCERT/CC participated in the cyber exercise “Locked Shields” organized by the NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE) during 13 – 16 April 2021. We joined as a member of Japan's Blue Team. This article describes how JPCERT/CC and other members participated in Locked Shields, its objectives, the value of the exercise, and challenges. What is “Locked Shields”? Locked Shields is the largest and most complex international live-fire cyber...
-
This blog post focuses on the 1st track of JSAC2021, following the previous reports on the 2nd and 3rd track.Opening Talk: Looking Back on the Incidents in 2020Speaker: Takayoshi Shiigi (JPCERT/CC)Slides (English)VideoTakayoshi opened the JSAC2021 with an overview of incidents that JPCERT/CC confirmed in 2020, focusing on targeted attack and widespread attack.Targeted attack in 2020 is characterised by leveraging cloud services for malware operation in multiple stages of attacks from...
-
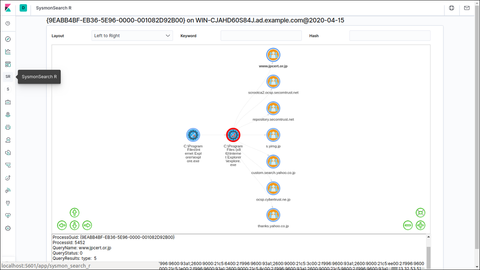
SysmonSearch is a tool developed by JPCERT/CC to analyse event logs generated on Sysmon (a Microsoft tool). https://github.com/JPCERTCC/SysmonSearch SysmonSearch is now compatible with Elastic Stack 7.x. Please note that the new version no longer supports Elastic Stack 6.x versions. This article introduces the new version of SysmonSearch, changes from the previous versions and new functions. Elastic Stack updates Kibana There was a change in Kibana plug-in due to the updates...