A shortcut file, also referred to as a shell link, is a system to launch applications or to allow linking among applications such as OLE. As we introduced in a previous blog post “Asruex: Malware Infecting through Shortcut Files”, shortcut flies are often used as a means to spread malware infection. Generally, shortcut files contain various types of information including the dates and environment that the shortcut file was created....
List of “朝長 秀誠 (Shusei Tomonaga)”
-
-
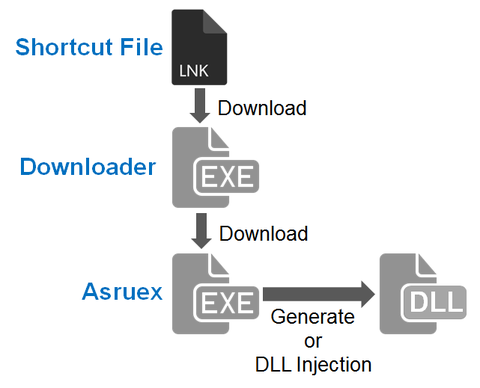
JPCERT/CC has been observing malicious shortcut files that are sent as email attachments to a limited range of organisations since around October 2015. When this shortcut file is opened, the host will be infected with malware called “Asruex”. The malware has a remote controlling function, and attackers sending these emails seem to attempt intruding into the targets’ network using the malware. According to a blog article by Microsoft, the malware...
-
Hello all, this is Shusei Tomonaga again. Generally speaking, malware analysis begins with classifying whether it is known malware or not. In order to make comparison with the enormous number of known malware samples in the database in a speedy manner, hash values are used, derived by performing hash functions to the malware sample. Among the different hash functions, traditional ones such as MD5 and SHA1 derive totally different hash...
-
Hello again, this is Shusei Tomonaga from the Analysis Center. In Windows OS, various commands (hereafter “Windows commands”) are installed by default. However, what is actually used by general users is just a small part of it. On the other hand, JPCERT/CC has observed that attackers intruding into a network also use Windows commands in order to collect information and/or to spread malware infection within the network. What is worth...
-
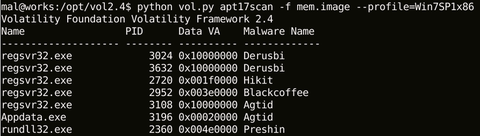
Hello again – this is Shusei Tomonaga from Analysis Center. This blog entry is to introduce “apt17scan.py” created by JPCERT/CC to detect certain malware used in targeted attacks, and to extract its configuration information. It is a plugin for the Volatility Framework (hereinafter “Volatility”), a memory forensics tool. My colleague Yuu Nakamura and I had the honour to introduce this at CODE BLUE 2015, an international conference for information security...
-
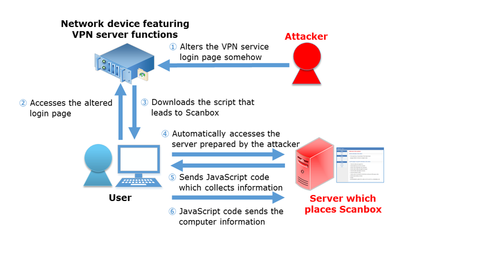
Hi, it’s Shusei Tomonaga again from the Analysis Center. JPCERT/CC has confirmed several attack cases around May 2015, which attempt to steal information of computers leveraging specific network devices featuring VPN server functions. The target of the reconnaissance varies from installed software to keylogs, and it is presumed that the attacker has aimed to steal such information from computers which attempt to login to VPN servers through altered login pages....
-
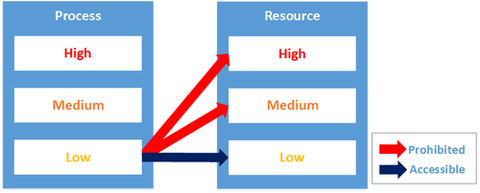
Hi, it’s Shusei Tomonaga again from the Analysis Center. My previous post discussed the mitigation effects against damages caused by malware infection by enabling Internet Explorer’s (hereafter “IE”’s) Protected Mode. In this article, I’d like to introduce an even stronger security function called “Enhanced Protected Mode”, which is a feature of IE 10 and 11 - its overview and preventive effects against damages caused by malware infection. OVERVIEW OF ENHANCED...
-
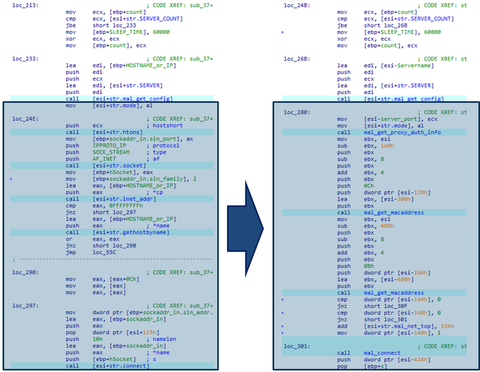
Hi, it’s Shusei Tomonaga again from the Analysis Center. PoisonIvy, a Remote Access Tool/Trojan (RAT) often used in targeted attacks, had been widely seen until around 2013. Since then, the number of cases using PoisonIvy in such attacks decreased, and there was no special variant with expanded features seen in the wild. However, recently, we have observed cases where PoisonIvy with expanded features in its communication function were used for...
-
Hello, this is Shusei Tomonaga again from the Analysis Center. JPCERT/CC has been observing cases where vulnerability in Internet Explorer (“IE” hereafter) is leveraged in targeted attacks, etc., resulting in system takeover or configuration change by a third party. In fact, IE has several functions to prevent such exploits. In this article, I will introduce one of the functions called “Protected Mode” – its overview and effects. OVERVIEW OF PROTECTED...
-
This is Shusei Tomonaga at Analysis Center. PlugX, a Remote Access Tool (RAT) often seen in many APT cases, has been in the wild for some years. Various sectors in Japan have been suffering from this type of attack from 2012, and Analysis Center has been working to catch up on the evolution of the PlugX family since then. In this blog post, I will write about a recent PlugX...